/TL;DR
Efficiently managing cyber security exposures and vulnerabilities is critical to keeping an organization’s most valuable assets secure. With cyber threats growing in complexity and volume, security teams are constantly challenged to manage an increasing workload while keeping risks at bay. Streamlining the vulnerability management lifecycle has never been more important. This blog will walk you through the 7 stages of this lifecycle and offer actionable tips for improving efficiency, ensuring your organization stays one step ahead of potential threats.
Why Does the Vulnerability Management Lifecycle Matter?
The vulnerability management lifecycle is a structured process designed to identify, prioritize, and address security vulnerabilities within an organization’s infrastructure. It plays a pivotal role in protecting businesses from cyber threats by ensuring that vulnerabilities are detected and remediated before they can be exploited. For security teams, efficiently navigating this lifecycle can make the difference between proactively managing risk and falling victim to an attack.
Ignoring identified vulnerabilities, especially critical ones, can lead to severe consequences. These include data breaches, financial losses, and reputational damage. The longer vulnerabilities remain unresolved, the greater the chance that malicious actors can exploit them.
A well-executed vulnerability management program helps organizations stay ahead of these risks. By consistently identifying and addressing vulnerabilities, security teams can maintain a strong defense and reduce the likelihood of security incidents.
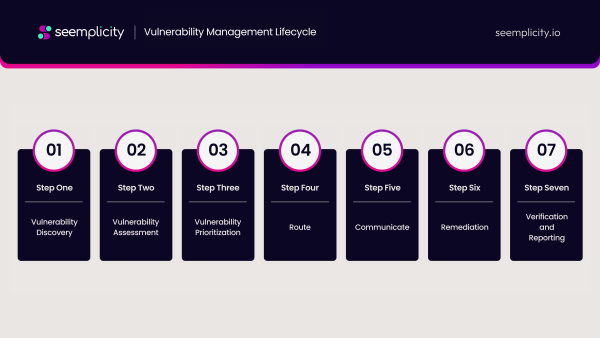
The 7 Stages of the Vulnerability Management Lifecycle
Effective vulnerability management is a multi-step process, designed to ensure security teams can identify, prioritize, and remediate vulnerabilities efficiently. Below are the seven key stages of the vulnerability management lifecycle, each critical to minimizing risk and strengthening an organization’s cybersecurity posture.
Vulnerability Discovery
The first step involves conducting comprehensive vulnerability testing doing vulnerability scans. These tools identify weaknesses within an organization’s systems and applications, scanning for potential points of exploitation. Regular testing allows security teams to detect vulnerabilities before they become a problem, forming the foundation of a solid vulnerability management process.
Vulnerability Assessment
Once vulnerabilities have been discovered, the next stage is vulnerability assessment, where the findings from the tests are analyzed. At this stage, security teams dig deeper into the vulnerabilities to understand their nature, potential impact, and where they exist within the system. Security teams may normalize and aggregate findings to better understand vulnerabilities and their required fixes, enabling a smoother process in the subsequent stages.
Vulnerability Prioritization
With many vulnerabilities uncovered, not all pose the same level of threat. Vulnerability prioritization focuses on ranking vulnerabilities based on their severity and business context. A combination of vulnerability scoring frameworks help organizations prioritize. For example, the Common Vulnerability Scoring System (CVSS) ranks vulnerabilities by severity, while Known Exploited Vulnerability (KEV) catalogs, such as those by CISA and VulnCheck, identify vulnerabilities that have been exploited in the wild, which indicate a higher criticality. The Exploit Predication Scoring System (EPPS) predicts which vulnerabilities are likely to get exploited, providing more real-time risk insights than CVSS, for example. Combining these scoring systems with business context enables organizations to assess vulnerabilities according to their specific environment and risk-capacity. By identifying critical vulnerabilities that represent the greatest risk to the organization, security teams can allocate resources to address the most dangerous issues first, ensuring the most urgent threats are handled promptly.
Route
At this stage, it’s crucial to route remediation tasks to the appropriate teams or individuals. This ensures that those responsible for fixing the vulnerabilities receive sufficient information and clear direction. Getting remediation requests to the right owners is essential for reducing delays and improving efficiency in the vulnerability management process.
Communicate
Collaboration between the security team and other stakeholders, such as development or IT teams, is one of the most critical, and perhaps underestimated success factors for addressing vulnerabilities efficiently. Seamless and bi-directional communication ensures that everyone is on the same page, with fixes being applied quickly and accurately. This stage enhances cross-team coordination, helping to streamline the overall remediation process.
Remediation
The remediation stage is the most critical step in the vulnerability management lifecycle, where the identified vulnerabilities are fixed, often through patches, configuration changes, or other security solutions. This stage is often the most challenging for organizations, due to inefficiencies in the previous stages. Ensuring that the remediation efforts are executed properly reduces the chance of exploitation, closing the gap that would otherwise be left open to threats.
Verification and Reporting
The final stage involves verifying that the remediation was successful. Verification and reporting are crucial to ensure that vulnerabilities have been effectively resolved and that no issues persist. Reporting on these outcomes not only keeps stakeholders informed but also helps in continuously refining the process for future cycles.
How to Navigate the Vulnerability Management Lifecycle More Efficiently
Efficiently managing vulnerabilities is critical to reducing security risks and keeping operations running smoothly. Below are some practical tips for improving the efficiency of the vulnerability management lifecycle, ensuring your team can address threats swiftly and effectively.
Adopt Automation
One of the most effective ways to speed up the vulnerability management process is by incorporating automation. Automated vulnerability scanners, vulnerability management workflows and remediation tools can significantly reduce the time it takes to assess systems, identify security weaknesses, open remediation tickets and apply fixes. This allows security teams to focus on higher-level decision-making and remediation, rather than getting bogged down by manual tasks.
Strengthen Collaboration
Fostering seamless collaboration between security teams and fixing teams, such as development and IT teams, is key to improving the remediation process. Regular communication and alignment across teams ensure that everyone involved understands their responsibilities, timelines, and the criticality of addressing vulnerabilities. Bi-directional feedback loops between security and fixing teams can also help identify bottlenecks and streamline workflows.
Ensure Clear Reporting
Clear reporting is essential to ensure that all stakeholders—whether technical or non-technical—understand the risks posed by critical vulnerabilities. Establishing transparent communication channels and creating easy-to-digest reports can help decision-makers prioritize resources more effectively. This ensures that everyone, from executives to engineers, is aligned on the steps being taken to reduce risk and improve the organization’s overall security posture.
Maintain Continuous Improvement
Efficiency in vulnerability management isn’t just about automation; it’s about learning from past efforts to improve future responses. Implementing a process of continuous improvement allows security teams to evaluate which remediation processes and methods were most effective and refine workflows over time. By analyzing metrics like remediation time, the number of recurring vulnerabilities, and compliance with SLAs, teams can ensure their vulnerability management lifecycle becomes more resilient and adaptive with each cycle.
These steps not only improve efficiency but also empower security teams to stay ahead of evolving threats.
What are the Benefits of Having an Efficient Vulnerability Management Program?
An efficient vulnerability management program offers numerous benefits to organizations, helping to secure critical assets while maintaining operational stability. By quickly identifying and remediating vulnerabilities before they can be exploited, security teams can prevent issues that might cause system outages or performance degradation. This means less unexpected downtime and less impact on business continuity, allowing organizations to keep their operations running smoothly without costly interruptions. Some key benefits include:
Better Resource Allocation
An optimized vulnerability management process enables security teams to better allocate their already strained resources. By prioritizing vulnerabilities based on business risk, teams can focus their efforts on addressing the most critical risks first, ensuring that time and resources aren’t wasted on less urgent issues. This approach leads to greater efficiency and more strategic use of security resources, helping organizations get the most out of their security investments.
Scalability
As organizations grow, new threats emerge, and the volume and complexity of vulnerabilities increase, making scalability a critical factor. A well-designed vulnerability management program scales effortlessly with the organization, enabling teams to manage thousands of vulnerabilities across different domains with the same resources as before, without losing efficiency.
Reduced Downtime
Efficient remediation of identified vulnerabilities minimizes system disruptions, ensuring that business operations continue smoothly. By quickly resolving issues, organizations can avoid costly downtime and maintain high levels of productivity.
Improved Security Posture
Proactively managing vulnerabilities significantly enhances an organization’s overall security posture. By addressing weaknesses before they can be exploited, security teams can minimize the risk of breaches and safeguard sensitive information, helping to stay one step ahead of cyber threats.
Cost Savings
Automation helps organizations get the most from their limited security resources by reducing the need for them to perform manual, tedious and error-prone work. Additionally, preventing security incidents through a well-structured vulnerability management program reduces the need for costly post-breach remediation. This not only helps avoid the financial impact of data breaches but also protects the organization’s reputation and customer trust.
Regulatory Compliance
With data privacy regulations becoming increasingly stringent, maintaining an effective vulnerability management program is crucial for ensuring compliance. Many regulatory frameworks, such as GDPR and HIPAA, mandate that organizations have robust vulnerability management practices in place. An efficient program ensures that organizations can meet these compliance requirements, avoid fines, and maintain a strong reputation in the marketplace.
Prioritize and Remediate Critical Vulnerabilities Easily with Seemplicity
Seemplicity’s platform is built to help security teams efficiently identify and prioritize critical vulnerabilities, allowing organizations to focus on the most significant risks without getting overwhelmed by the sheer volume of data.
The platform automatically consolidates, deduplicates, normalizes and aggregates findings, eliminating noise and ensuring security teams can compare vulnerabilities accurately. The platform enriches vulnerability data with insights from threat intelligence sources and internal business-context, allowing teams to understand which vulnerabilities pose the greatest business risk. By doing so, Seemplicity empowers teams to make informed decisions and focus attention on high-impact vulnerabilities. This is especially useful for security teams managing large IT ecosystems or those dealing with multiple attack surfaces, such as cloud, code and infrastructure environments.
Seemplicity’s AI-powered technology provides teams with tailored remediation plans. By integrating with the organization’s existing tools and workflow systems, Seemplicity automatically routes actionable remediation tasks to the right fixing teams in the work platforms they already use, significantly reducing the time it takes to respond to critical vulnerabilities. The platform’s collaborative capabilities further enhance efficiency by ensuring seamless communication between security, development, and operations teams, leading to faster resolution times.
With Seemplicity, organizations can streamline their remediation operations, reduce risk exposure, and improve overall operational efficiency by ensuring that critical vulnerabilities are prioritized and remediated in a timely manner.
Schedule a demo today to learn more about how Seemplicity’s platform can accelerate risk reduction and enhance the efficiency of your security team.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.