CTEM execution, powered by AI
Unify scoping, discovery, prioritization, validation, and mobilization into one continuous system, turning fragmented signals into a clear path to action.
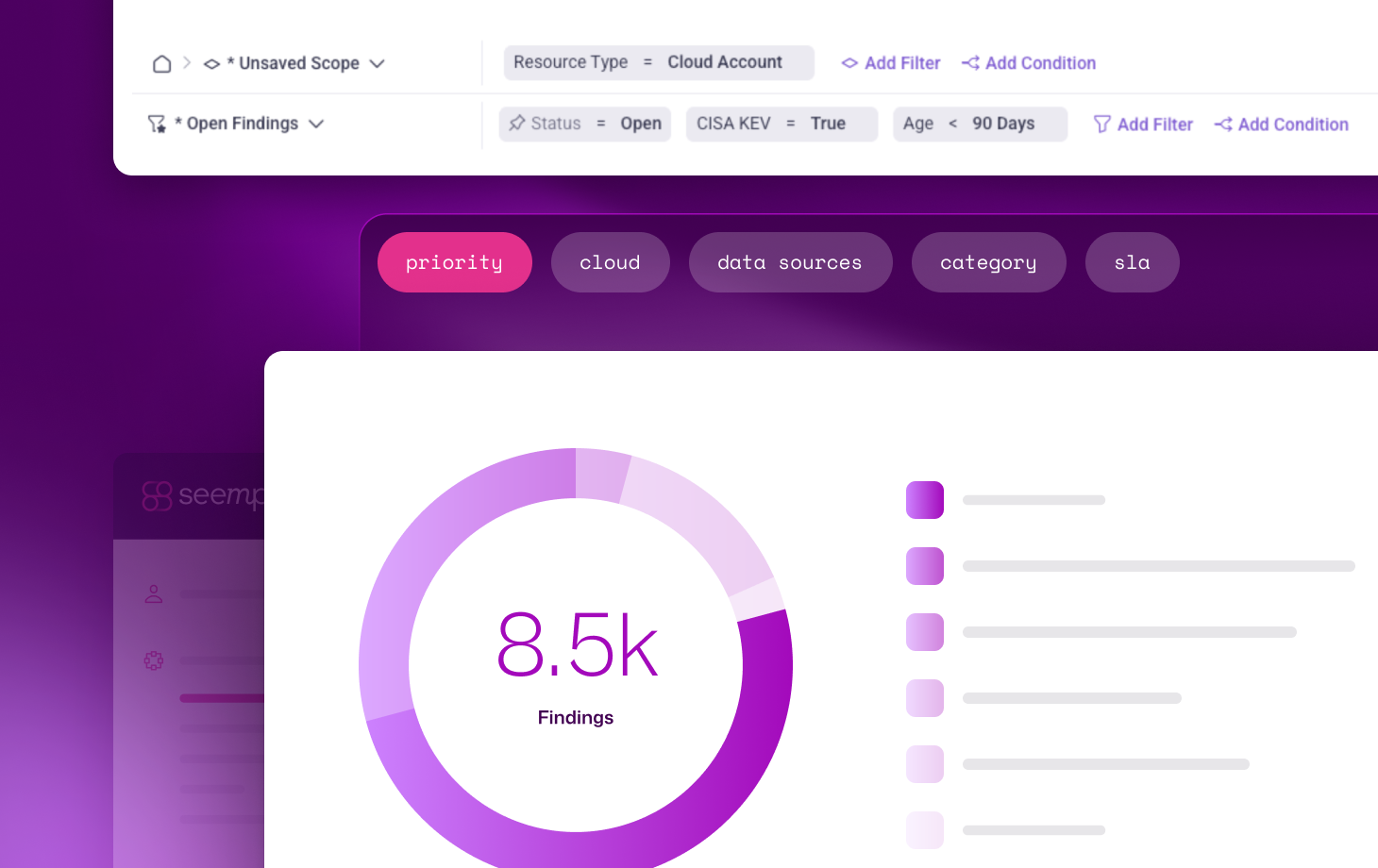
Continuous scoping across your entire attack surface
Maintain an always-current view of what matters. Normalize asset data across disparate tools and environments to define the true scope of your exposure landscape.
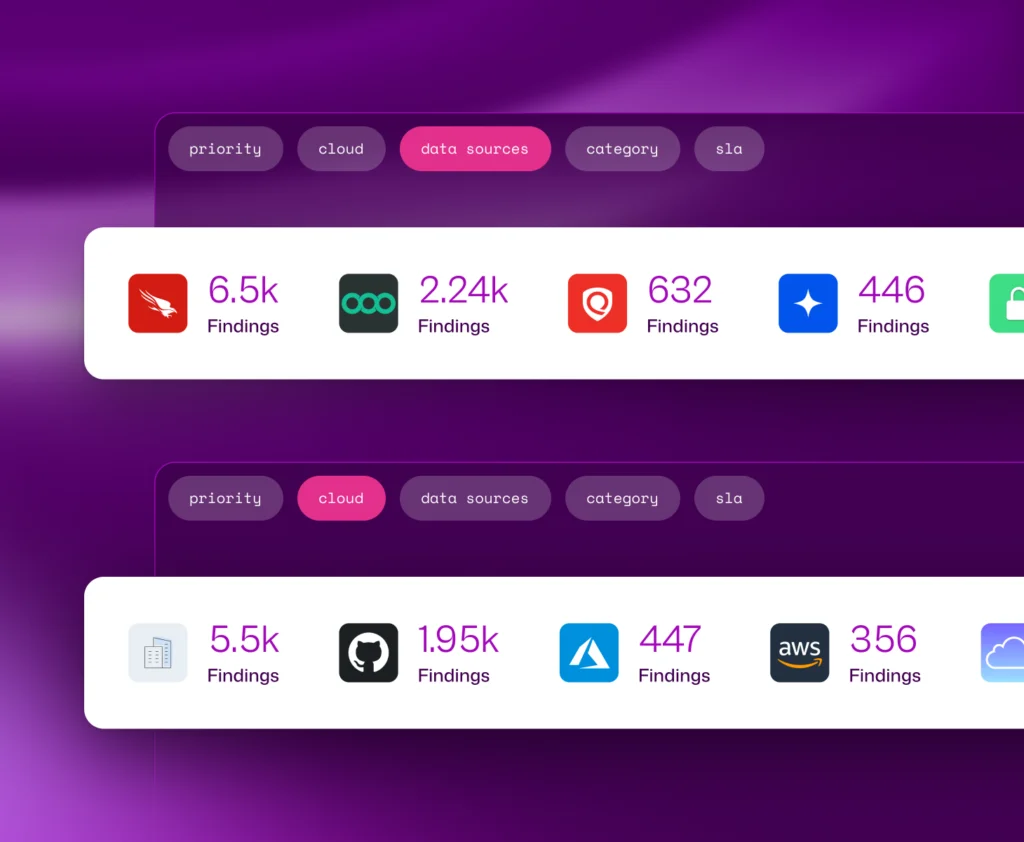
Comprehensive discovery without blind spots
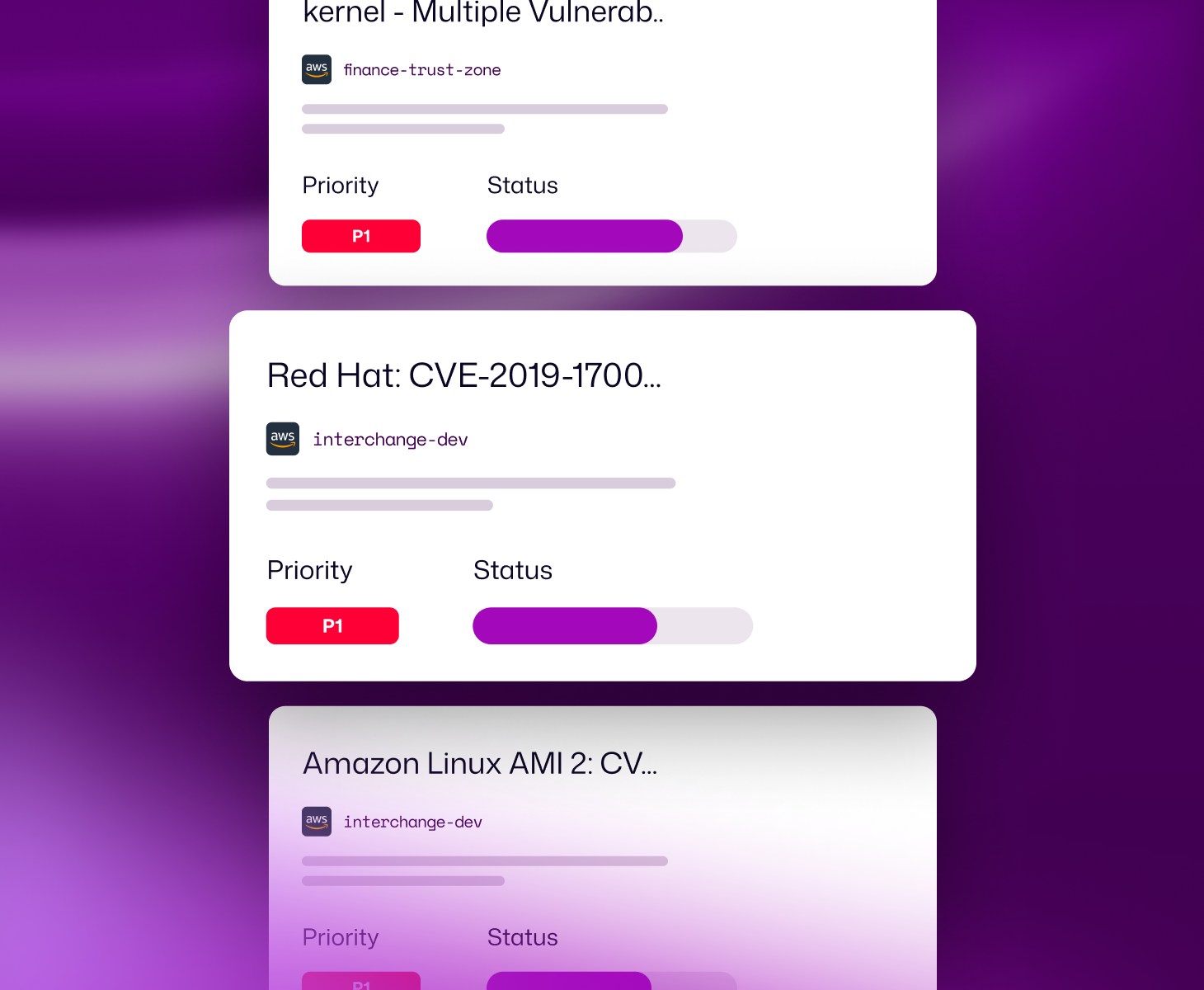
Risk-based prioritization that reflects real-world exposure
Reachability validation built for you
Mobilization that drives remediation at scale
Real results for teams of every size.
Assets without owners
%
%
Critical findings resolved
%
%
Finding backlogs reduced
K
K
Remediation velocity
Weeks
Days
The platform purpose-built for CTEM operationalization
Unify and normalize your exposure data
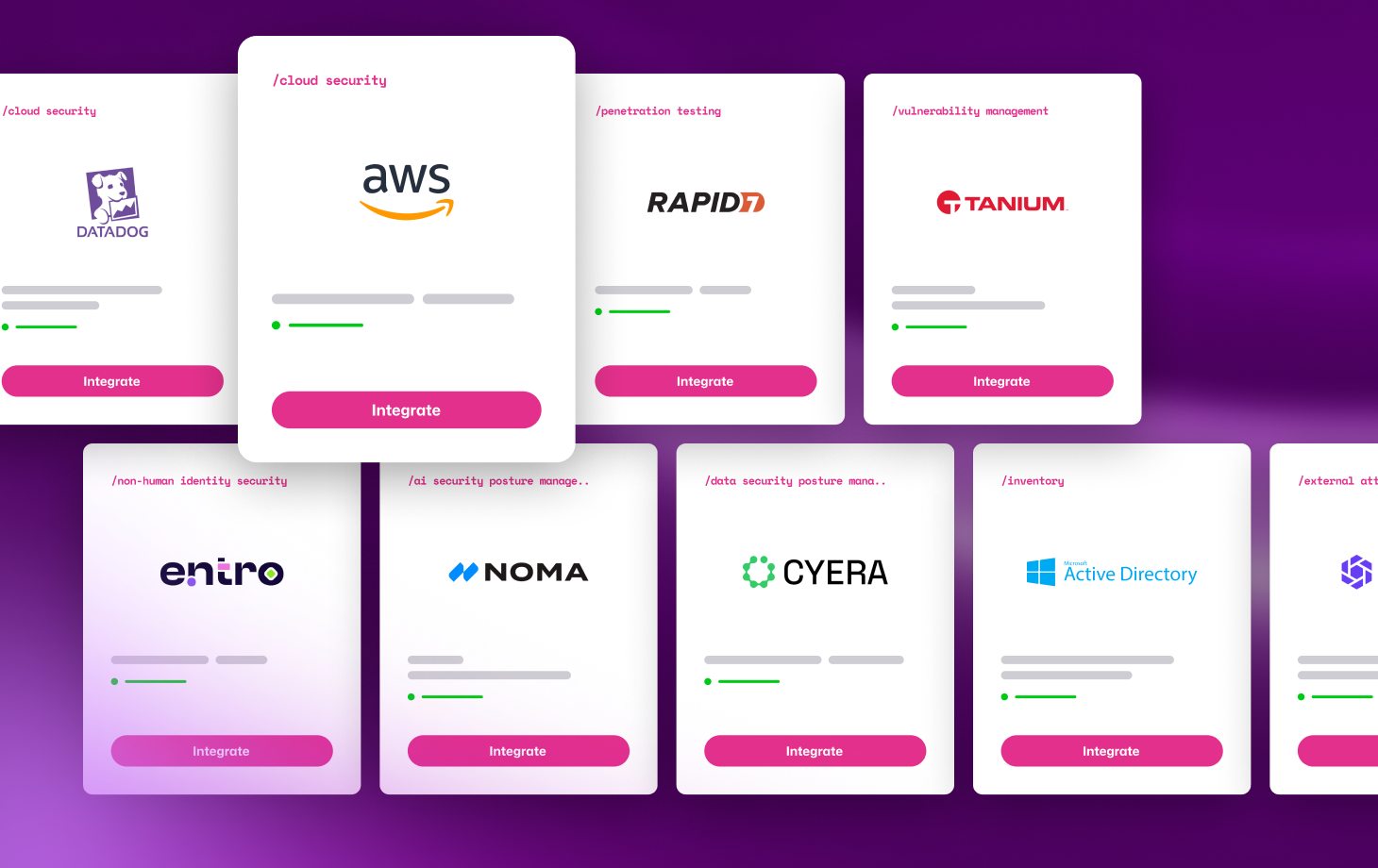
Ingest data from scanners, CNAPPs, ASM, and more into a single, consistent model. Eliminate fragmentation and create a reliable foundation for your CTEM program.
AI agent teams drive remediation forward
Specialized AI agents validate exposures, assign ownership, and route fix-ready tasks directly into existing workflows, eliminating manual handoffs and keeping execution moving.
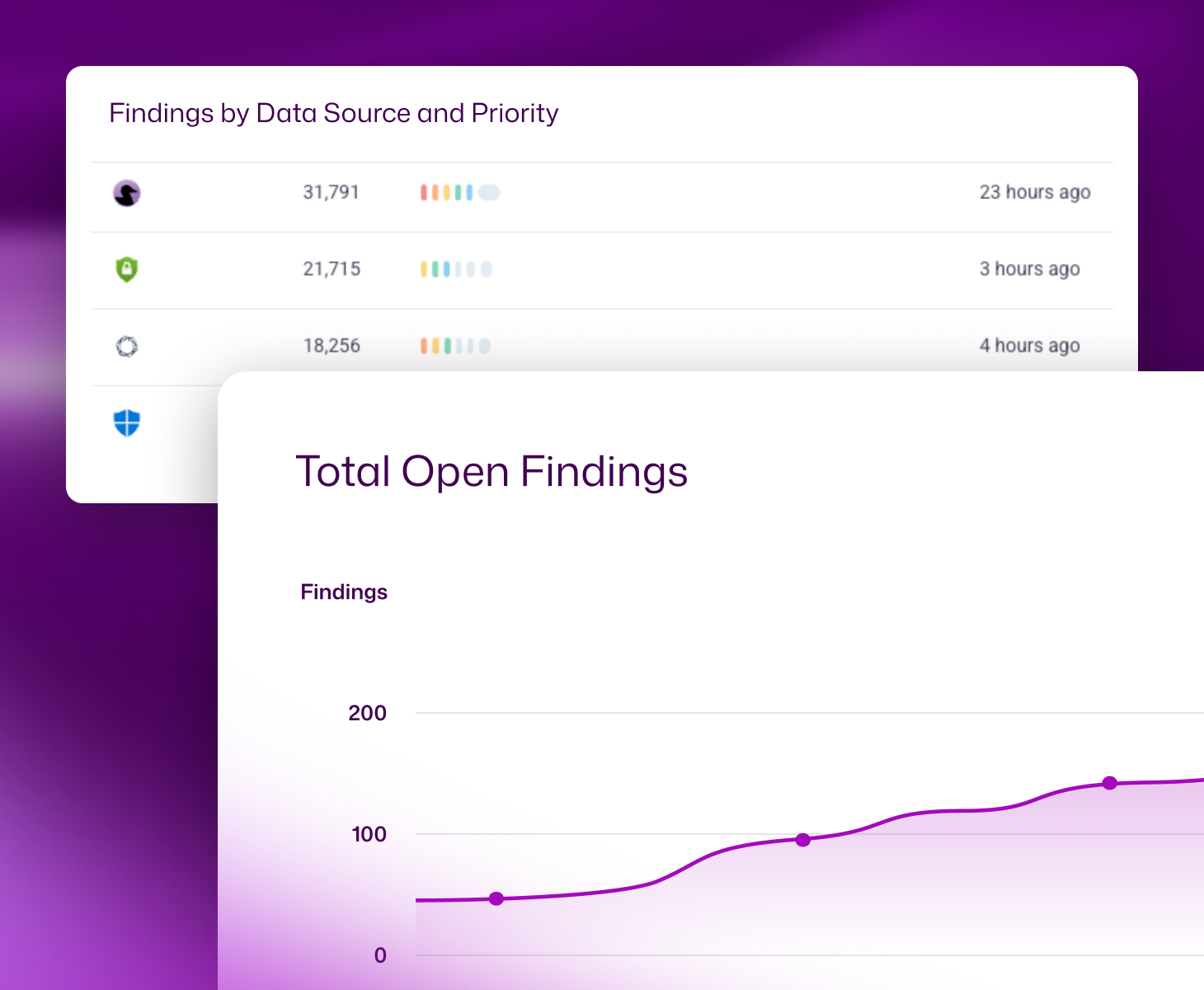
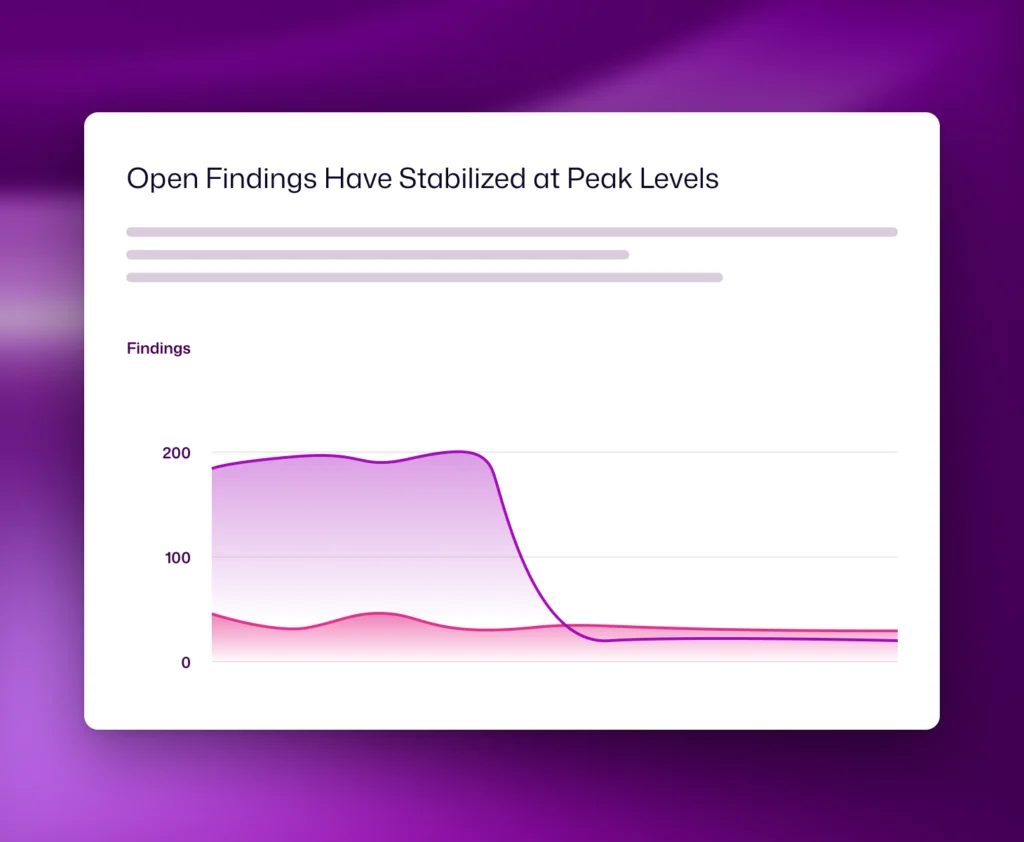
See risk go down, not just activity go up
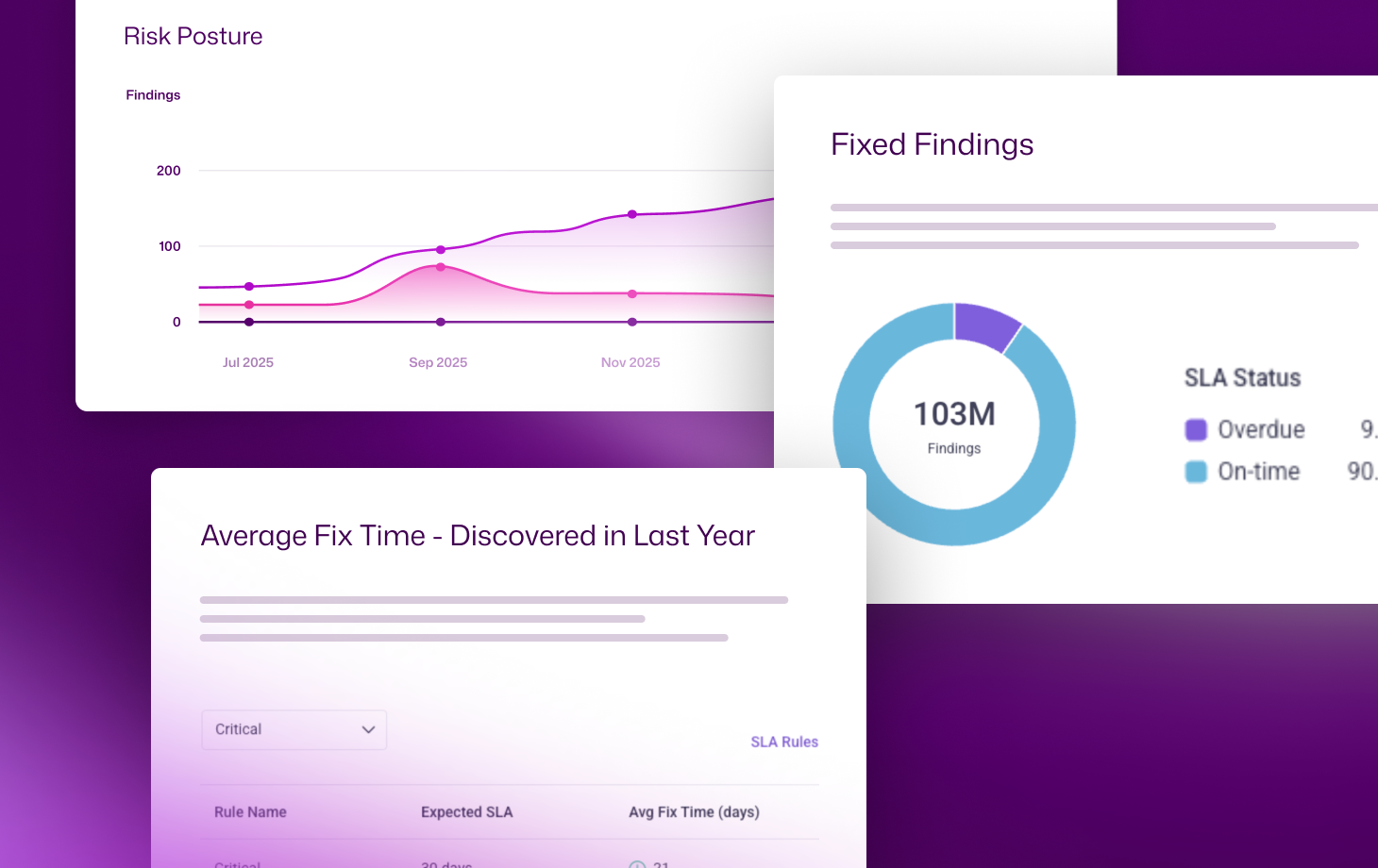
Most programs measure output. We measure impact. Track how exposures are actually reduced over time with live metrics that prove your CTEM program is working.

/research Report
2026 Exposure Action Report
Real exposure management insights based on 2025 customer data. Learn how teams scale remediation, reduce backlogs, and drive measurable risk reduction.
Say Goodbye to
Backlog of vulnerabilities
Misconfigurations
Scattered findings across tools