/TL;DR
The second annual Remediation Operations Report from Seemplicity paints a clear picture: while organizations are investing more in security, they’re not necessarily getting faster or more effective at fixing what matters.
This year’s data highlights a growing gap between strategic intent and day-to-day execution. Security leaders want to move faster, collaborate better, and prioritize smarter. But process bottlenecks and legacy workflows keep getting in the way.
In the sections that follow, we’ll break down the biggest themes from the research: the disconnect between budget increases and operational improvements, the challenges of effective prioritization, and the mounting pressure to scale automation and collaboration. Because if we want to improve remediation, we have to start by fixing how we fix things.
Security Spending Is Up; but Efficiency Hasn’t Caught Up
In 2025, security budgets are trending upward. According to the report, 86% of organizations increased their security spending this year, signaling a strong commitment to addressing growing cyber risk. However, while funding is available, financial constraints remain a top concern. Nearly one-third of organizations cite budget limitations as their primary barrier to adopting new vulnerability management tools.
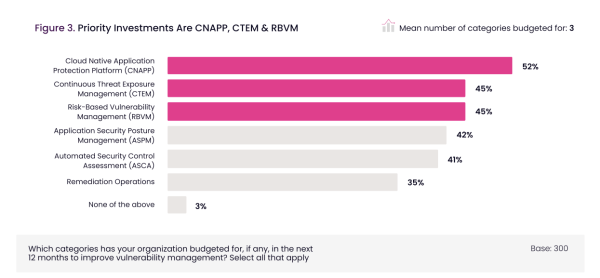
At the same time, many organizations are expanding their security stacks. On average, respondents plan to adopt three new vulnerability and exposure management tools in 2025. Investments are concentrated in areas like Cloud-Native Application Protection Platforms (CNAPP) (52%), Continuous Threat Exposure Management (CTEM) (45%), and Risk-Based Vulnerability Management (RBVM) (45%). This points to a growing preference for consolidated platforms and continuous assessment – encouraging signs of a more strategic, long-term approach to security.
Metrics Are Maturing, But Vulnerability Management Challenges Persist
Organizations are becoming more intentional in how they define and track the success of their vulnerability management programs. While 61% of respondents still rely on the number of vulnerabilities resolved as a primary metric, more meaningful measures are gaining traction. Breach reduction (54%) and mean-time-to-remediate (MTTR) (49%) now rank as the second and third most-used metrics, reflecting a broader shift toward measurable outcomes over activity.
However, better metrics haven’t eliminated the core challenges that make vulnerability management so difficult in practice. According to the research, the most common barrier security teams face is making findings actionable for development and operations teams (41%). Closely following that is poor collaboration between security and development (40%), which directly impacts the clarity and execution of remediation efforts. And not far behind, 34% of organizations cite difficulty prioritizing vulnerabilities as a major obstacle.
In short: despite the growing use of more strategic success metrics, many organizations still lack the foundational processes needed to improve against those metrics in a meaningful way.
Prioritization Gaps Are Slowing Everything Down
With prioritization already identified as a core challenge in vulnerability management, the data offers deeper insight into why this continues to be such a persistent issue, and what’s standing in the way of improvement.
While many organizations have adopted prioritization frameworks, most still rely heavily on threat intelligence feeds (47%) and internal priority scores (46%). These methods provide valuable context, especially when tuned to an organization’s specific risk profile. However, the report reveals that the most effective approaches – structured, data-driven models like VulnCheck KEV, EPSS, and CISA KEV – are significantly underutilized.
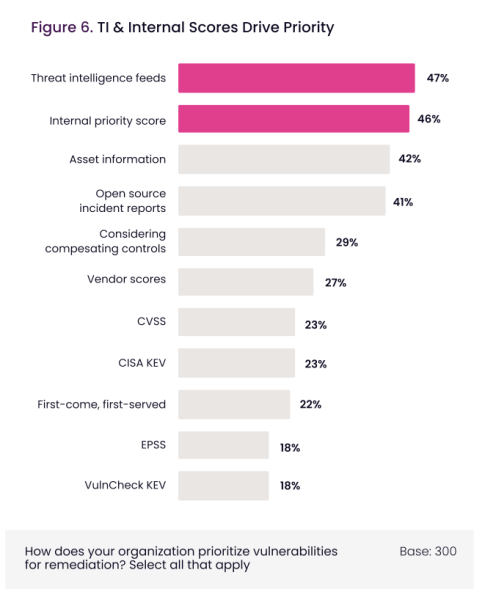
Despite being rated as >95% effective by respondents, these structured models remain the exception, not the norm. For example, only 18% of organizations report using EPSS and VulnCheck KEV. By contrast, 22% still rely on a “first come, first served” approach, an unstructured method ranked as the least effective in the report. The fact that this outdated tactic is used nearly as often as CISA KEV (23%) underscores a fundamental misalignment between what teams know works and what they actually implement.
This gap in adoption likely stems from a mix of factors: limited awareness of emerging models, perceived complexity in implementation, or assumptions that these methods won’t apply to their specific environment. Whatever the cause, the result is the same: prioritization efforts that lack consistency and fail to align remediation efforts with true risk. In turn, time and resources are spent on lower-impact issues while critical vulnerabilities remain unresolved. This contributes directly to slower remediation, increased exposure windows, and friction across teams.
The Noise Problem: Too Many Alerts, Too Little Clarity
When security teams are flooded with alerts – many of which are low priority or duplicative – it becomes harder to separate the signal from the noise, delaying meaningful action. According to the report, 90% of organizations report challenges managing excessive alert volume, up 5% from the previous year. The top three challenges were partial visibility of actual risk (41%), slow risk reduction efforts (35%), and lack of process compliance (35%).
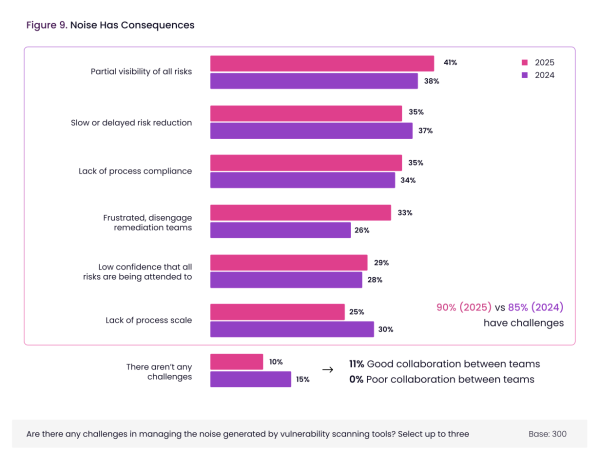
The data also reveals a clear connection between noise and team dynamics. Organizations with strong cross-team collaboration are far less likely to struggle with noise-related issues. In fact, 11% of organizations with high collaboration report no noise challenges at all, compared to 0% of organizations with poor collaboration. This correlation highlights how effective coordination and shared context can reduce cognitive overload and improve decision-making under pressure.
Perhaps more importantly, noise isn’t just an upstream problem for security teams – it slows down the entire remediation pipeline. The report shows that organizations dealing with high noise levels take an average of two additional days to remediate critical vulnerabilities compared to those with low noise. That delay has significant implications for exposure time, risk posture, and operational resilience.
Collaboration Is Overestimated and Under-Engineered
While 85% of organizations believe they collaborate well across security, development, and operations, the data tells a more nuanced story. Many of the delays and inefficiencies reported in the research trace back to weak communication, misaligned priorities, and fragmented workflows.
With 91% of organizations experiencing remediation delays, the top cited cause was collaboration and communication challenges, named by 31% of respondents. That’s nearly twice as high as the next most common barrier – manual processes (19%). This underscores just how much of the vulnerability management burden is organizational rather than technical.
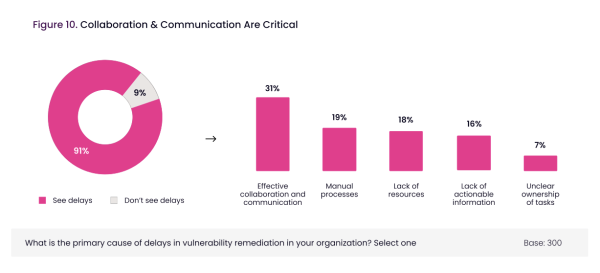
At a more granular level, the data reveals that long-standing points of friction between security and engineering remain unresolved. Tight development deadlines (26%) and misaligned priorities (23%) are the leading barriers to collaboration. These tensions are compounded by a lack of actionable security context (22%), leaving developers unclear on which issues truly require urgent attention. That aligns with what we’ve seen elsewhere in the data: when security findings aren’t made actionable, remediation slows down, and risk accumulates.
Even the mechanics of task assignment reveal inefficiencies. While 39% of organizations automatically assign remediation tasks via workflow tools, the majority (61%) still rely on manual task assignment or self-assignment – approaches that introduce ambiguity, delays, and inconsistency. The data shows a clear link between these outdated task-routing practices and poor collaboration outcomes. For example, 60% of organizations with weak collaboration still rely on manual task assignment, compared to much lower rates (29%) among those with stronger alignment.
How teams communicate also matters. Real-time chat (59%) and regular cross-team meetings (57%) are the most common collaboration methods, but they’re inherently ad hoc. Nearly half of organizations still lack a centralized system for managing remediation collaboration, resulting in siloed conversations and disjointed workflows. And yet, among those not using a centralized platform today, 99% express interest in adopting one; an unmistakable signal that teams recognize the need for more structured coordination.
Automation and AI: High Adoption, Low Maturity
As security programs continue to grow in complexity, automation and AI are increasingly viewed as critical tools for reducing inefficiencies and scaling operations. Nearly all organizations (97%) report some level of automation in their vulnerability management processes, a clear sign that automation is no longer a “nice to have,” but a baseline capability.
And yet, despite this near-universal adoption, maturity is lagging. The percentage of organizations reporting fully automated workflows actually dropped in 2025, going from 41% last year to just 35% this year. This decline suggests that while most teams are automating something, few have achieved end-to-end automation across the vulnerability lifecycle. Manual intervention remains widespread: nearly 40% of respondents say more than half of their vulnerability management process is still manual.
Where automation is implemented, the benefits are clear. Faster response times top the list (58%), followed by improved accuracy (57%) and reduced manual error (48%). These gains fundamentally reshape how teams work, enabling them to shift from reactive triage to proactive risk reduction.
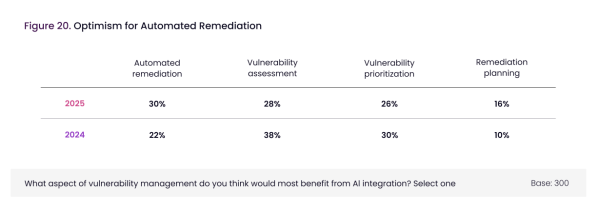
AI, in particular, is emerging as a critical lever for bridging this automation maturity gap. When asked where AI could have the greatest impact, respondents pointed most often to automated remediation, up from 22% in 2024 to 30% this year, making it the top-ranked use case.
Other emerging areas for AI include remediation planning, which saw a 60% increase year-over-year (from 10% to 16%). This suggests that organizations are starting to think beyond detection and toward more intelligent coordination, helping teams decide what to fix, when, and how.
Importantly, AI investment isn’t slowing down. A full 88% of organizations plan to increase their AI spend over the next five years, up slightly from last year. While the growth rate is modest, the consistency of this trend points to increasing confidence in AI’s role – not as a replacement for human expertise, but as an accelerator for complex, resource-constrained workflows.apibus.
Where to Focus Improvement Efforts
The 2025 Remediation Operations Report highlights clear areas where organizations can drive meaningful change. Progress won’t come just from more tools, it will come from better execution. Here’s where to focus:
- Adopt structured, risk-based prioritization models: Incorporate proven approaches like EPSS, VulnCheck KEV, and CISA KEV into workflows to ensure critical issues are addressed first, replacing guesswork with high-confidence decisions.
- Strengthen cross-team collaboration through purpose-built workflows: Move beyond chat threads and meetings. Centralize task ownership, provide actionable context to developers, and align teams with shared systems and processes.
- Scale automation across the entire remediation lifecycle: Expand automation beyond scanning. Automate triage, task routing, and tracking to eliminate manual bottlenecks and improve time to remediation.
- Leverage AI to improve execution – not just detection: Focus AI investments on automated remediation planning, where they can reduce workload and increase consistency, especially in complex environments.
Each of these focus areas targets a core bottleneck identified in the research. Together, they offer a practical roadmap to reduce exposure time, improve coordination, and turn remediation into a true engine of security resilience.
Conclusion: Fixing the Fixing Process
The state of remediation operations in 2025 reflects a broader truth about cybersecurity: knowing what’s vulnerable isn’t the hard part anymore – acting on it effectively and efficiently is.
The data shows clear momentum in the right areas. Budgets are increasing. Metrics are evolving. Teams are exploring automation and AI with more purpose. But without the operational backbone – structured prioritization, centralized collaboration, and end-to-end execution – those efforts can’t scale.
What’s slowing teams down isn’t a lack of intent or capability. It’s fragmentation:
- Tools that don’t connect.
- Workflows that aren’t aligned.
- Teams that aren’t speaking the same language when it comes to risk.
Fixing that requires more than incremental adjustments. It requires treating remediation as a core operational discipline, not just a reactive follow-up to vulnerability detection. That means investing in the processes that drive speed, consistency, and clarity across functions.
Ultimately, the organizations that succeed won’t necessarily be the ones with the most tools. They’ll be the ones that fix things better. Not faster for the sake of speed, but smarter, with greater precision, alignment, and confidence.
Remediation operations isn’t just about closing tickets. It’s about closing the gap between risk and resolution consistently, sustainably, and at scale.
To unlock even more insights, read the full report here.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.




