/TL;DR
As digital threats grow increasingly sophisticated, organizations must stay ahead by adopting advanced strategies to manage and mitigate vulnerabilities. This necessity has driven significant changes in how remediation operations are conducted, emphasizing the importance of continuous improvement and innovation.
Seemplicity’s 2024 Remediation Operations Report revealed several key trends and practices that are shaping the future of remediation operations. This blog post will outline some of these developments, highlighting how evolving threats are influencing remediation strategies and the steps organizations can take to fortify their defenses.
Key Findings
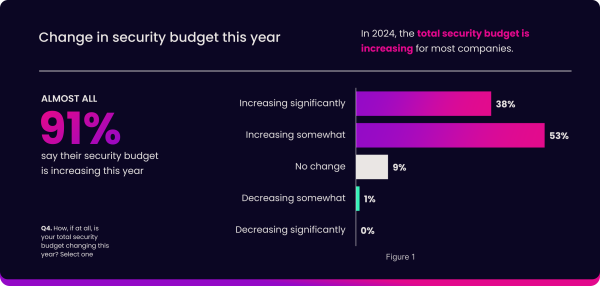
Growing Budgets for Cybersecurity
One of the most notable trends in 2024 is the substantial increase in security investments. According to the report, 91%of respondents have reported an increase in their security budgets, reflecting a growing recognition of the importance of robust cybersecurity measures.
High-profile incidents, such as the SolarWinds breach, have highlighted the critical need for enhanced security measures. This case set a precedent, prompting organizations to allocate more resources to safeguard their assets and maintain stakeholder trust.
Complexity and Fragmentation in Security Tools
As organizations strive to strengthen their security posture, many have adopted a multi-vendor approach, utilizing an average of 38 different security product vendors.
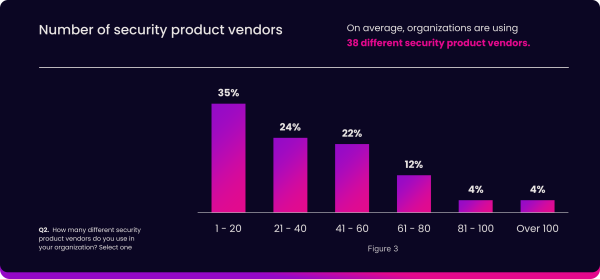
While this strategy can address various aspects of security needs, it also introduces complexity and fragmentation. Managing such a diverse set of tools poses significant challenges in terms of integration, interoperability, and the overall efficacy of the security infrastructure.
The Challenge of Security Tool Noise
A significant issue that organizations face is the excessive noise generated by all their security tools. The report indicates that 51% of respondents experience high levels of noise, inundating security teams with alerts, notifications, and findings.
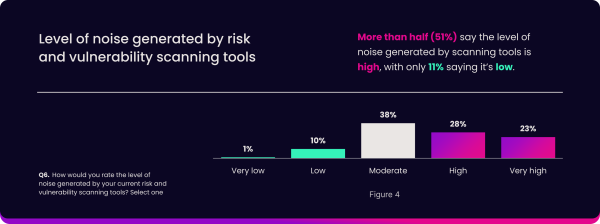
Moreover, 85% of respondents find it challenging to manage this noise, with the slow pace of risk reduction being a top concern.
Adoption of CTEM Framework
In response to these challenges, many organizations are turning to the Continuous Threat Exposure Management (CTEM) framework.
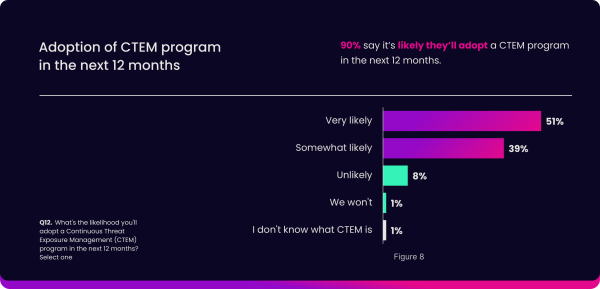
The report reveals that 90% of respondents are likely to adopt CTEM programs, reflecting a shift towards continuous monitoring and proactive risk management. Unlike traditional periodic assessments, CTEM enables organizations to stay ahead of threats by continuously monitoring their IT infrastructure for vulnerabilities.
Enhanced Efficiency through Automation
Automation is increasingly being recognized as a critical component in enhancing vulnerability management efficiency. The report highlights that 97% of respondents indicate some level of automation within their processes.
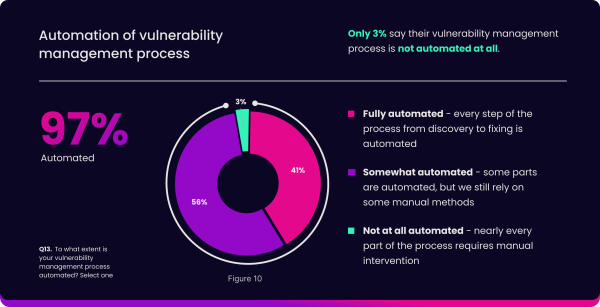
For 89% of respondents, the adoption of automation has improved efficiency, with 65% of respondents reporting faster threat response times as the top benefit.
By automating routine tasks, organizations can focus their efforts on more strategic aspects of cybersecurity, thereby improving overall resilience.
Increasing Investment in AI
Artificial Intelligence (AI) is playing an increasingly vital role in cybersecurity, with 85% of respondents planning to increase their AI investment over the next five years.
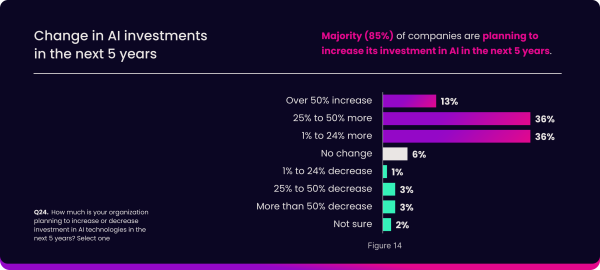
AI is expected to have a significant impact on vulnerability assessment (38%) and prioritization (30%), helping organizations streamline their processes and focus on addressing the most critical security risks.
However, there are concerns about the rapid pace of AI integration and its potential impact on the pace of vulnerability management, highlighting the need for balanced and strategic implementation.
Embracing the Future
The landscape of remediation operations is rapidly evolving. By understanding and embracing these trends, organizations can enhance their remediation strategies and build more resilient security postures. For a comprehensive understanding of these developments, download the full report and stay ahead of the evolving threats in 2024.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.




