Let’s be real—spreadsheets have been the go-to tool for vulnerability management for years. They’re easy to set up, familiar, and flexible. But here’s the hard truth: they’re costing you time, accuracy, and security.
Imagine trying to track thousands of vulnerabilities across an ever-changing attack surface using a tool designed for budgeting, not security. Spreadsheets don’t scale, they don’t update in real time, and they don’t help your team act fast when a critical vulnerability emerges. Worse, we’ve seen companies dedicate entire full-time employees just to maintain these unwieldy, error-prone files—time that should be spent fixing issues, not babysitting a spreadsheet.
Cyber threats move fast. If your vulnerability management process is stuck in a manual, outdated workflow, it’s not a matter of if you’ll fall behind—it’s when. It’s time to move on.
Let’s highlight some of the reasons why spreadsheets are no longer serving you when it comes to identifying, prioritizing, and communicating vulnerabilities.
1. Spreadsheets Are a Full-Time Job—Literally
We had a customer who had an entire full-time employee dedicated to maintaining their vulnerability spreadsheet—week after week, doing nothing but updating, sorting, and sharing data. That’s 40+ hours a week just managing a spreadsheet.
Think about that: instead of focusing on fixing vulnerabilities, this person was stuck in an endless loop of data entry. And they’re not alone. Many organizations waste valuable time just trying to keep up—time that could be better spent on actual remediation.
What organizations really need is a scalable, automated system that eliminates manual data entry and streamlines vulnerability management. With real-time updates and integrated workflows, get back to focusing on what matters instead of maintaining spreadsheets.
2. Manual Tracking Is a Disaster Waiting to Happen
Spreadsheets require constant updates, and mistakes are inevitable. A simple copy-paste error or a missed update can mean the difference between fixing a critical vulnerability and leaving your organization exposed.
CISA’s Cyber Resilience Review emphasizes the need for continuous and repeatable vulnerability management processes. The problem? Spreadsheets weren’t built for automation or real-time updates.
A centralized platform will ensure accuracy, consistency, and repeatability. By automating data collection and tracking, organizations can reduce human error, maintain a clear audit trail, and confidently close vulnerabilities before they become breaches.
3. Collaboration Shouldn’t Feel Like a Game of Telephone
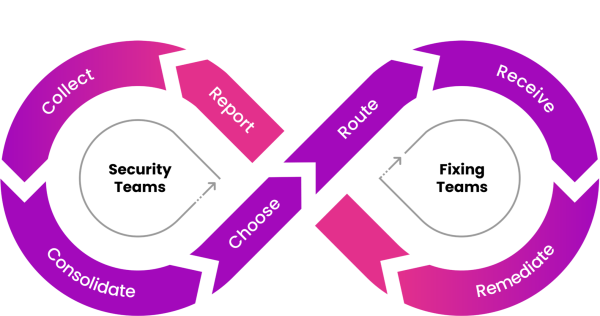
Security and IT teams need to work together in real time to identify, prioritize, and patch vulnerabilities. But spreadsheets? They don’t make that easy. Version control issues, multiple copies floating around, and confusion over who updated what—it’s inefficient, slows remediation, and creates unnecessary frustration.
Research from Forrester confirms that security teams with strong collaboration and engagement experience fewer breaches. A modern vulnerability management platform eliminates these barriers by providing real-time updates, task assignments, and progress tracking. No more emailing spreadsheets back and forth.
By streamlining collaboration, security, IT, and development teams can focus on remediation instead of administrative overhead, reducing risk more effectively.
As Gartner eloquently put it, “Organizations need consistent processes that feed well-established paths for IT teams and other business units to mobilize fixes. To be successful, security teams must not only find problems but also focus on designing a mechanism to apply fixes.”
4. Prioritization Is More Than Just Sorting a Column
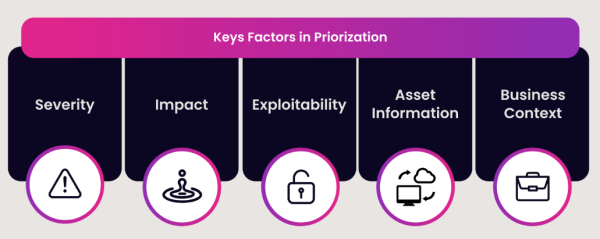
Not all vulnerabilities are equal, and treating them that way leads to wasted effort and increased risk. Sorting by CVSS or EPSS scores alone lacks the intelligence needed to determine real-world urgency.
Prioritization isn’t just about severity—it’s about context. A high CVSS score doesn’t always mean immediate risk, and a low one doesn’t guarantee safety. Without factoring in exploitability, asset criticality, and business impact—like whether a system is internet-facing or holds sensitive data—you risk fixing the wrong things first.
Effective vulnerability and exposure management requires automation, real-time threat intelligence, and dynamic business context. If you’re still relying on a spreadsheet, you’re just reorganizing data—not prioritizing risk. An intelligent prioritization engine incorporates real-time threat intelligence, asset criticality, and business context, ensuring teams focus on the vulnerabilities that matter most.
5. Spreadsheets Don’t Scale—Your Business Does
As your organization grows, so does your attack surface. More assets. More vulnerabilities. More complexity. Yet, your spreadsheet stays the same—getting longer, harder to manage, and increasingly ineffective.

Managing vulnerabilities this way doesn’t just slow down security teams—it also pulls development teams away from product innovation, forcing them to spend valuable time deciphering static spreadsheets instead of building and improving your core business offerings.
Modern vulnerability and exposure management platforms are built to scale. They integrate with scanners, ticketing systems, and security tools, providing an always-updated, real-time view of risk across your environment. With a streamlined, automated approach, security teams can drive remediation efficiently, and development teams can stay focused on what they do best—delivering innovation.
The Bottom Line: It’s Time to Move On
Spreadsheets had their moment, but they’re simply not built for today’s challenges. They slow remediation efforts, create bottlenecks, and pull teams away from critical security initiatives. The time, effort, and headcount spent maintaining them could be better used to actively reduce risk—not just document it. Security teams need speed, visibility, and automation to stay ahead of threats, and that’s exactly what a modern vulnerability remediation platform delivers.
Say Goodbye to Spreadsheets, and Hello to Efficiency with Seemplicity
With Seemplicity, you can:
- Automate your entire vulnerability management workflow: Eliminate manual data entry and fragmented tracking by consolidating remediation efforts in one platform. Seemplicity automates the entire vulnerability management lifecycle—from findings collection and correlation to prioritization, ticket creation, status updates, and progress tracking—ensuring vulnerabilities move seamlessly from detection to resolution. With intelligent workflows, teams can enforce remediation SLAs, minimize administrative overhead, and focus on what matters most: reducing risk faster.
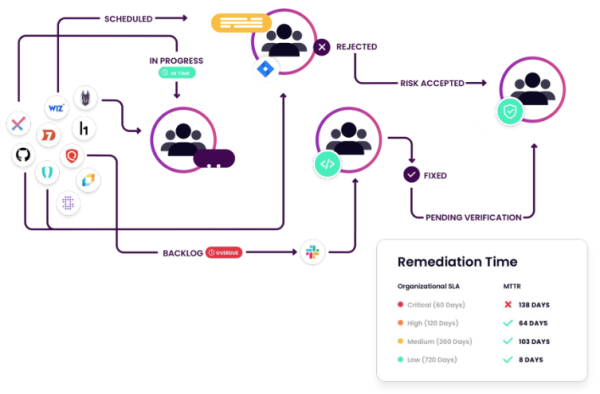
- Achieve real-time visibility across all assets: Get a continuously updated, centralized view of vulnerabilities across your entire attack surface. Seemplicity integrates with your scanners, asset management tools, and security solutions – over 100, to be exact – to ensure you always have a clear picture of which vulnerabilities to prioritize and who needs to be notified. Security teams gain instant clarity on critical vulnerabilities, while IT and engineering teams receive prioritized, contextualized remediation tasks within their existing workflows, ensuring the right vulnerabilities are addressed by the right teams at the right time.
- Prioritize with intelligence and business context: Move beyond static risk scores and surface-level severity ratings. Seemplicity enhances prioritization by factoring in exploitability, asset criticality, and business impact, ensuring teams focus on vulnerabilities that pose the greatest real-world risk. Whether a vulnerability affects internet-facing systems, critical infrastructure, or sensitive data, Seemplicity dynamically adjusts risk levels and directs remediation efforts where they matter most
- Scale seamlessly across teams and tools: Manage vulnerabilities at any scale without increasing operational overhead. Seemplicity connects with your existing scanners, ticketing systems, and security tools, creating a frictionless, end-to-end remediation process. Whether you’re handling thousands or millions of vulnerabilities, automation ensures that security and IT teams stay aligned, remediation efforts remain trackable, and SLAs are met without manual intervention.
- Enable frictionless collaboration: Break down silos between security, IT, and engineering by centralizing communication and workflow execution. With automated workflows, real-time updates, clear task ownership, and bi-directional integrations with ticketing systems like Jira and ServiceNow, Seemplicity ensures remediation efforts are aligned, efficient, and bottleneck-free. Teams receive actionable remediation plans with full context, reducing back-and-forth inquiries and expediting time to resolution.
Security shouldn’t be a spreadsheet exercise. The right tools empower your team to focus on what truly matters: remediating vulnerabilities faster and strengthening your security posture without disrupting business initiatives.
Ready to move beyond spreadsheets? See how Seemplicity can transform your security operations. Watch our Seemplicity RemOps Platform demo today.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.