/TL;DR
The role of vulnerability management has never been more critical, especially as professionals in the field face the daunting task of securing entire organizations with minimal budget and headcount. Seemplicity’s recent on-demand webinar highlighted that despite the number of Common Vulnerabilities and Exposures (CVEs) and Common Weakness Enumerations (CWEs) increasing each year, many organizations are not proportionately augmenting their vulnerability management teams, leading to an imbalance between the remediation workload and available resources. As the volume of vulnerabilities continues to grow, vulnerability management teams are on the lookout for realistic methods to make their workloads manageable.
This situation demands more innovative approaches to vulnerability management, leveraging automation and advanced analytics to streamline processes and improve efficiency. By focusing on high-impact vulnerabilities and optimizing remediation workflows, remediation teams can ensure that they address the most critical threats first without being overwhelmed by sheer numbers. Enhancing visibility, communication, and automation will empower these teams to handle the escalating volume of vulnerabilities more efficiently, which is essential for securing organizations in an increasingly complex threat landscape.
CTEM – A New Approach for Vulnerability Management Visibility
Gartner’s Continuous Threat Exposure Management (CTEM) framework represents a fresh and effective approach to vulnerability management. By emphasizing a continuous, adaptive process, CTEM enables organizations to manage vulnerabilities proactively rather than reactively. This framework is designed to help organizations increase visibility of emerging threats by continuously evaluating and improving their security posture, addressing vulnerabilities as they arise, and ensuring that remediation efforts are both timely and effective.
The CTEM framework has quickly become a top technology trend for 2024, particularly as organizations face increasing challenges such as a lack of visibility across their expanding attack surfaces, difficulty in tracking siloed technologies, and identifying responsible parties for remediation. The growing reliance on third-party technologies introduces further complexity to the vulnerability management process. By adopting CTEM, organizations will be better enabled to address security challenges head-on and maintain an effective defense against potential threats.
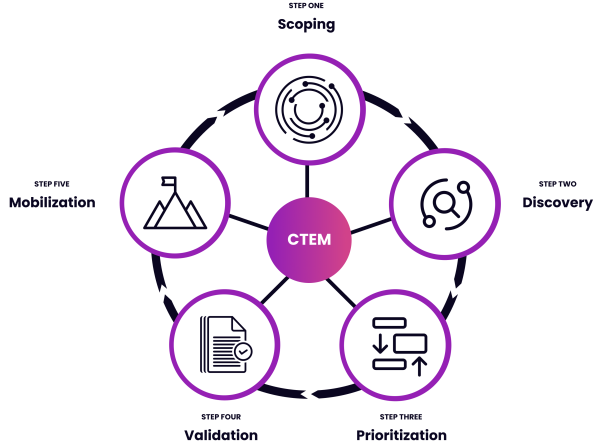
Seemplicity’s Remediation Operations platform is well-aligned with the five steps of the CTEM framework, making it an ideal solution for organizations looking to implement this innovative approach.
Seemplicity aids mobilization by transforming risk and vulnerability data into automated workflows and actionable remediation tasks, ensuring that teams can respond swiftly and efficiently.
Seemplicity helps teams scope their environment by tagging each asset, enabling flexible and precise scoping.
Seemplicity facilitates the discovery of risks by collecting, normalizing, deduplicating, and aggregating findings from various risk assessment tools.
Prioritization is streamlined based on data source, risk severity, ticket status, and fixing team, ensuring that the most critical vulnerabilities are addressed first.
Validation is supported through integration with assessment tools like Breach & Attack Simulation (BAS) and Pen Testing as a Service (PTAAS), as well as bi-directional integration with work management and ticketing systems.
Poor Communication is a Bottleneck
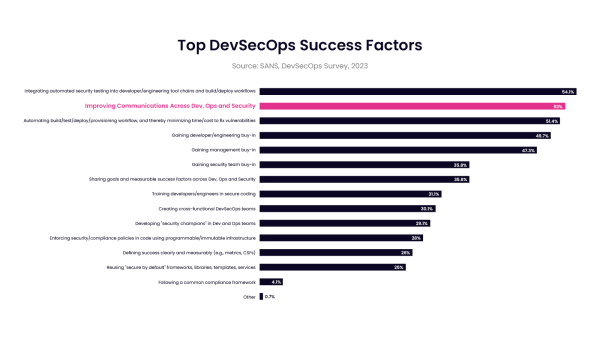
Poor communication stands as a significant bottleneck in the remediation process, often leading to delays and inefficiencies that can heighten organizational risk. The SANS DevSecOps Survey has consistently identified “improving communication across dev, ops, and security” as a top success factor for three consecutive years, underscoring the critical need for effective communication channels. When communication is fragmented across siloed departments, it becomes challenging to coordinate efforts, share vital information, and make informed decisions promptly.
The difficulty in communication between siloed departments often leads to indecision on remediation next steps, causing unnecessary delays. This indecision not only hampers the speed of addressing vulnerabilities but also increases the window of exposure, giving potential attackers more time to exploit known weaknesses. Waiting on approvals before taking action further exacerbates this issue, as the time spent navigating bureaucratic hurdles and obtaining necessary sign-offs can significantly slow down the remediation process, leaving the organization vulnerable for longer periods.
Effective communication is vital for successful remediation operations, and remediation operations platforms worth their salt provide a unified source of communication and coordination for remediation teams. By ensuring clear coordination, a remediation operations platform eliminates indecision and streamlines the entire process. It facilitates efficient back-and-forth communication between responsible parties, allowing teams to quickly address and resolve vulnerabilities. With consistent and reliable communication of status updates and other relevant remediation information, a remediation operations platform ensures that all stakeholders are informed and aligned, driving faster and more effective vulnerability management.
Automation in the Right Places
Manual Processes
Automation can drastically improve remediation processes by streamlining workflows and reducing the inefficiencies associated with manual tasks. This allows security teams to focus on more strategic issues, rather than getting bogged down in repetitive tasks. Automation ensures that routine procedures are executed flawlessly and swiftly, making the entire remediation process more efficient and effective.
Workflows
Integrating automation into remediation workflows brings order to what can often be a chaotic process. It reduces work disruptions by providing clear ownership of next steps, ensuring that each team member knows their responsibilities and deadlines. This clarity prevents duplication of effort, as automated systems can track and manage findings coming in from separate tools and make sure multiple people aren’t working on the same issue unknowingly. The result is a more coordinated and streamlined approach to addressing vulnerabilities.
Process Compliance
Process compliance is another area where automation proves invaluable. By creating a unified process spanning all teams involved in remediation, automation provides consistent visibility into the status of remediation efforts. This visibility is crucial for monitoring ad-hoc and manual processes, ensuring that all steps are followed according to established protocols. Automation not only enforces compliance but also reduces the time and effort required to achieve it, freeing up resources to focus on other critical tasks.
Incident Response
Incident response workloads benefit greatly from automation of remediation workflows as well. Automated systems can help identify and fix bugs before they escalate into major problems, effectively preventing potential exploits that would have to be dealt with by incident response teams. By catching and addressing issues early, security teams end up spending less money than they would have dealing with a breach. This proactive approach not only mitigates risks but also enhances the overall security posture of the organization.
Ramp Up Vulnerability Management Practices
Enhanced visibility, better communication, and intelligent automation are vital to maximizing efficiency in vulnerability management, especially when resources are limited. Implementing the CTEM framework provides the enhanced visibility needed to stay ahead of emerging threats, ensuring that organizations can continuously monitor and address vulnerabilities. By avoiding communication bottlenecks through a robust Remediation Operations Platform like Seemplicity, teams can coordinate more effectively, reducing delays and improving response times. Intelligent automation drastically streamlines the remediation process, saving time, effort, and money by eliminating manual tasks and ensuring that vulnerabilities are addressed swiftly and accurately. Together, these strategies fortify comprehensive security measures, ensuring that organizations can effectively protect against cyber threats, even with constrained resources.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.




