/TL;DR
We’ve all seen it happen: you create a solid remediation plan, map out the misconfigurations and vulnerabilities, and develop a plan to fix them, but when it comes time to execute, things start to fall apart. Why do remediation plans fail even when they seem solid on paper? The truth is, it’s often not the plan itself, but how it’s executed. Let’s break down the common obstacles that cause remediation efforts to go wrong and what you can do to avoid them.
1. No One Knows Who’s Responsible for What
The Obstacle: One of the biggest reasons remediation plans fail is very straightforward: no one knows who’s responsible for what. Tasks fall through the cracks because assignments are too vague, and ownership isn’t clearly defined. People assume someone else is handling things, and before you know it, vulnerabilities are left unaddressed.
The Fix: Make sure that every workflow associated with fixing a finding has a specific owner. Be clear about who’s doing what, and use a system to keep track of progress. When people know they’re responsible, things get done. For example, each Developer should have their own remediation queue to help them focus on what matters most for them. Accountability is key!
2. Underestimating How Complex Things Are
The Obstacle: Sometimes, remediation plans fail because they overlook just how complicated the systems and teams really are. People often think they can solve issues quickly without considering all the dependencies and potential disruptions along the way. If you don’t fully grasp these complexities, your plan is going to fall apart.
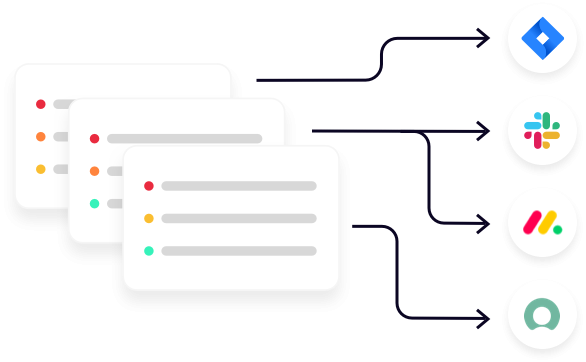
The Fix: Slow down and take a step back before diving in. Talk to everyone involved, understand the systems they’re working with, and don’t underestimate the complexity. Make sure your plan factors in all the dependencies, potential downtime, and any other challenges that could come up. It might take a little longer to plan, but it’ll save you from bigger headaches later. Once you’re confident you’ve identified all the key people, tools, and potential roadblocks, implementing a unified vulnerability management solution with seamless integrations for your organization’s existing tools can make executing your plan far smoother.
3. Relying Too Much on Manual Processes
The Obstacle: If your remediation plan relies heavily on manual tasks, you’re inviting trouble. Manual processes take time, they’re prone to human error, and they’re just not scalable. When managing a large number of vulnerabilities, this approach can quickly become overwhelming and lead to communication gaps.
The Fix: Automate as much as possible! Use a platform that leverages automation to do the work that so many teams do manually today: consolidate, normalize and deduplicate all security findings, prioritize fixes, create tickets, and assign responsibilities. This way, your team can focus on more strategic tasks, while vulnerabilities can be addressed faster and more efficiently. Automation is your friend here.
4. Fixing the Wrong Things First
The Obstacle: Not all vulnerabilities are equally dangerous, but too often, teams address them as if they are – by not prioritizing the right way. This means you might be spending time fixing something that seems urgent while bigger, more critical risks go unresolved.
The Fix: Take a risk-based approach to remediation by prioritizing vulnerabilities based on their potential impact and the likelihood of exploitation, incorporating risk scoring frameworks like the Common Vulnerability Scoring System (CVSS) and Exploit Prediction Scoring System (EPSS). You should also include business context, not just technical severity, to ensure vulnerabilities are prioritized according to your specific environment. Leverage automated tools to prioritize fixes, ensuring the most critical issues are addressed first. Focus on what poses the greatest risk, not just what’s easiest to fix, and deliver this information to fixing teams in a way that integrates smoothly into their workflows without causing disruptions or overwhelming them.
5. Not Enough Resources
The Obstacle: Most security and fixing teams face the challenge of managing too many vulnerabilities with limited resources. Whether due to staff shortages, tight budgets, or insufficient tools, staying on top of remediation can be difficult. This strain often leads to delays in patching and increased security risks, making it essential to prioritize critical vulnerabilities and find ways to work efficiently with what’s available.
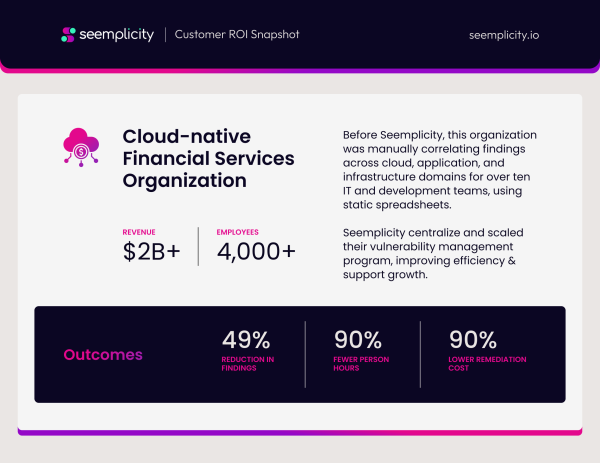
The Fix: Maximize the impact of your available resources by providing fixing teams with a consolidated queue of prioritized, actionable items. This approach helps ensure they focus on the right tasks and make confident decisions quickly. Tools that enhance efficiency can significantly improve performance. For example, one organization that partnered with us at Seemplicity reduced findings by 49%, cut labor hours by 90%, and lowered remediation costs by 90%. These results were achieved through capabilities like consolidating common findings into a single fix and automating the prioritization and handoff of items from the security team to the appropriate individual on the fixing team.
6. Fear of Disrupting Business
The Obstacle: Sometimes, organizations delay remediation efforts because they’re worried about disrupting critical business operations. No one wants to be the person who brings down the system during a peak business period, so security fixes get pushed to the back burner.
The Fix: Work closely with business stakeholders to find ways to minimize disruption and incorporate them into your prioritization efforts (as discussed in Section 4). Assess which systems are most critical and determine the best approach for remediation. This may involve scheduling patches for high-risk vulnerabilities in non-critical systems during peak periods or planning fixes for critical systems during off-peak hours. Phased rollouts can further reduce disruption.
To align remediation with business needs, clearly communicate the risks of delaying fixes to business leaders. Striking the right balance and incorporating these factors into your prioritization strategy ensures that high-risk vulnerabilities are addressed with minimal impact on business operations.
7. Process Compliance is an Afterthought
The Obstacle: In regulated industries, remediation efforts can be complicated by the need to meet compliance deadlines. This can lead to tension between the security team, which is focused on addressing the biggest risks, and the compliance team, which is trying to meet regulatory requirements.
The Fix: Align your remediation plan with compliance requirements from the start. Make sure your efforts are hitting both security and regulatory goals, so you’re not having to choose one over the other. Integrating compliance checks into your remediation workflow makes sure nothing falls through the cracks.
8. Not Monitoring Continuously
The Obstacle: If you’re not continuously monitoring your environment, new vulnerabilities or failed remediation can pop up, and you won’t even know about it until it’s too late.
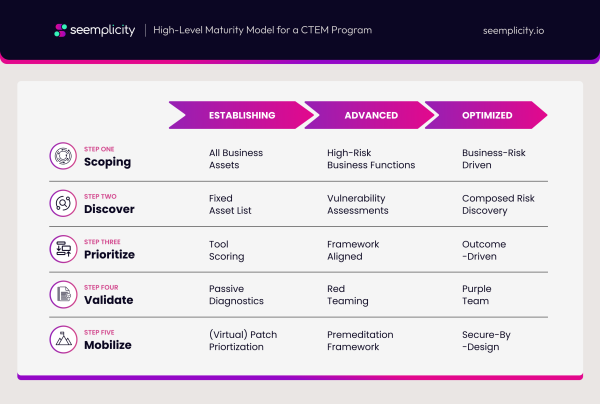
The Fix: Implement a Continuous Threat Exposure Management (CTEM) program, and keep an eye on things 24/7 with complementary solutions. This way, you can spot new vulnerabilities and verify that previous remediation efforts are holding up. It’s about staying proactive and making sure nothing slips through the cracks after your initial remediation efforts. SANS has provided guidance on how to successfully implement a CTEM program.
The Bottom Line
Remediation plans don’t fail because they’re bad plans; they fail because executing them is tough. From unclear roles to poor communication and limited resources, there are a lot of factors that can derail even the best-laid plans. But by focusing on clear ownership, communication, automation, and continuous threat exposure management, you can dramatically improve your remediation plan execution. After all, it’s not just about having a plan – it’s about ensuring it works when you need it most.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.




