AI-driven AppSec to fix what matters, faster
Normalize, prioritize, and automate your application security workflow. Turn a sea of AppSec findings into a single, fix-ready request that your developers will actually implement.
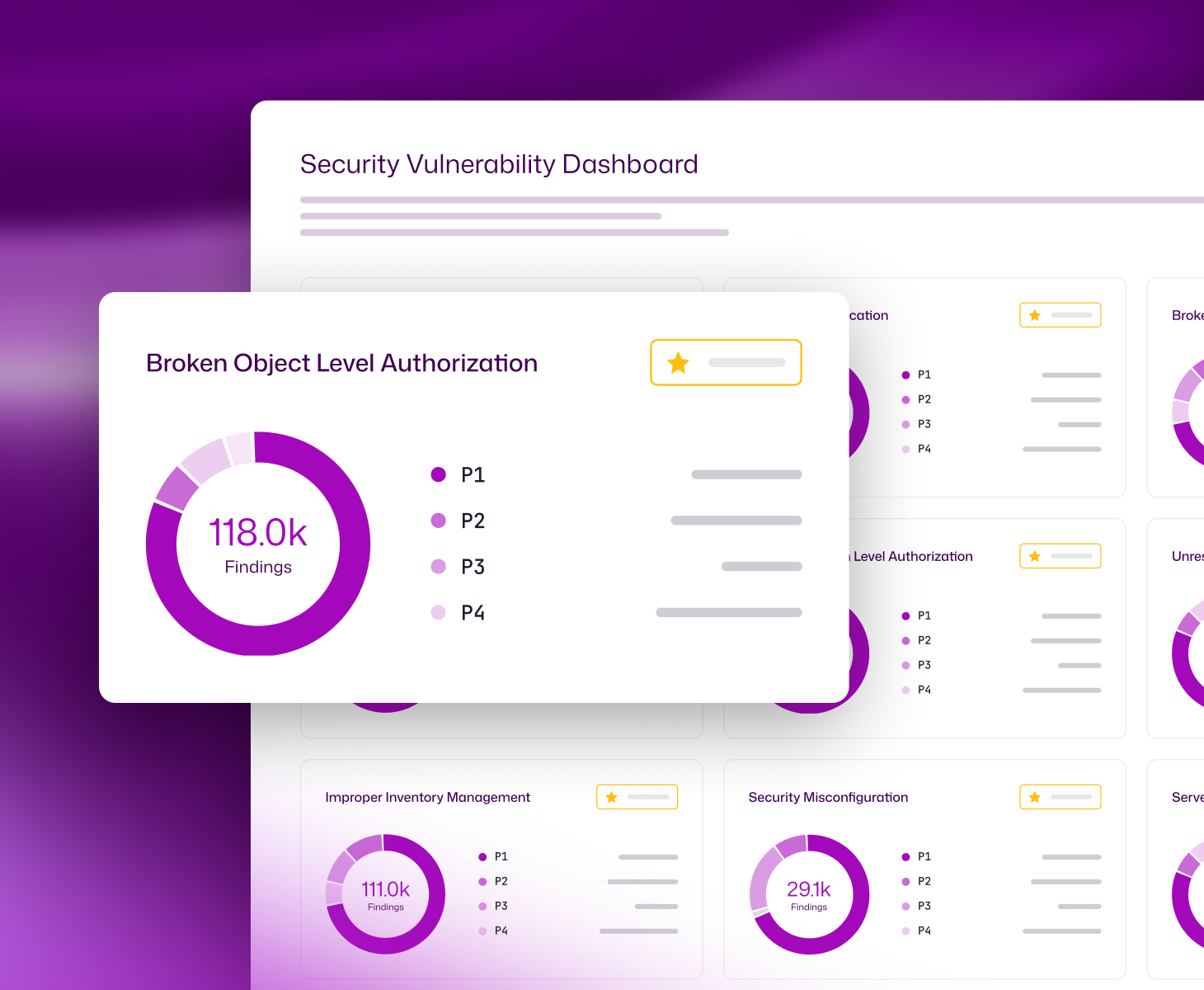
Unified, contextualized AppSec visibility
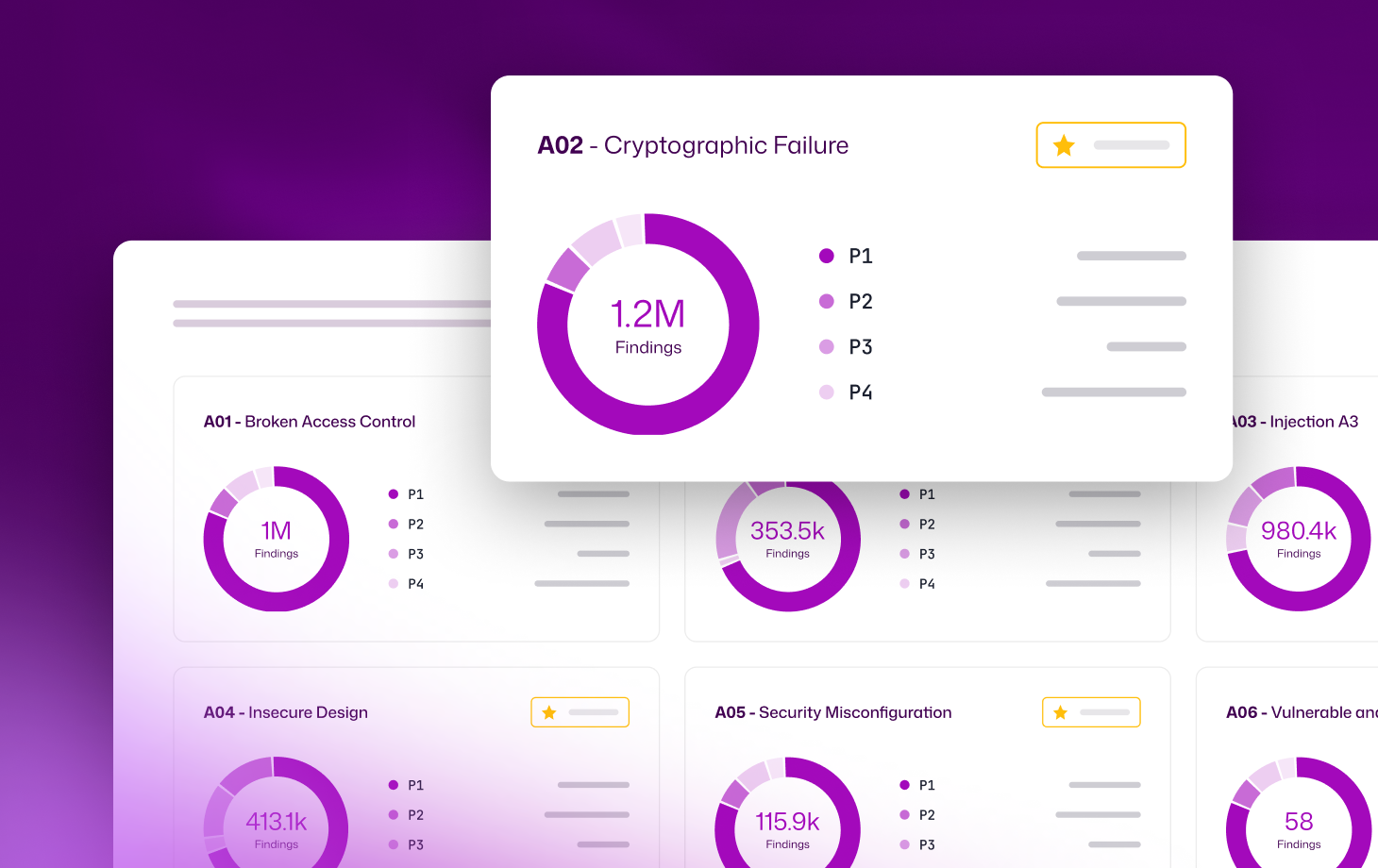
Don’t just aggregate data; normalize it. Get a single, comprehensive view of your entire application security posture. Integrate and correlate findings from SAST, DAST, SCA, IAST, and API security tools to eliminate blind spots and normalize risk data across your code and running apps.
Prioritize AppSec flaws with true business context

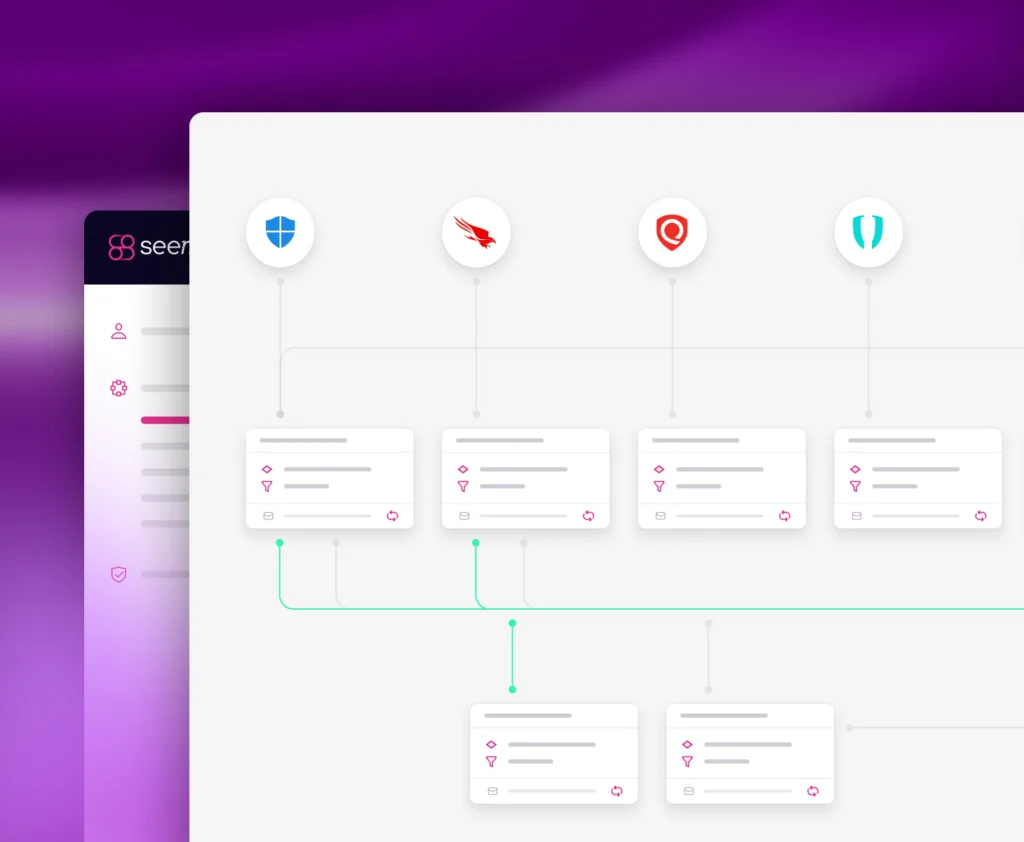
Automate mobilization from detection to deployment
Continuous validation and tracking
Real results for teams of every size.
Assets without owners
%
%
Critical findings resolved
%
%
Finding backlogs reduced
K
K
Remediation velocity
Weeks
Days
A complete solution for AppSec exposure management
Centralize and normalize your exposure data
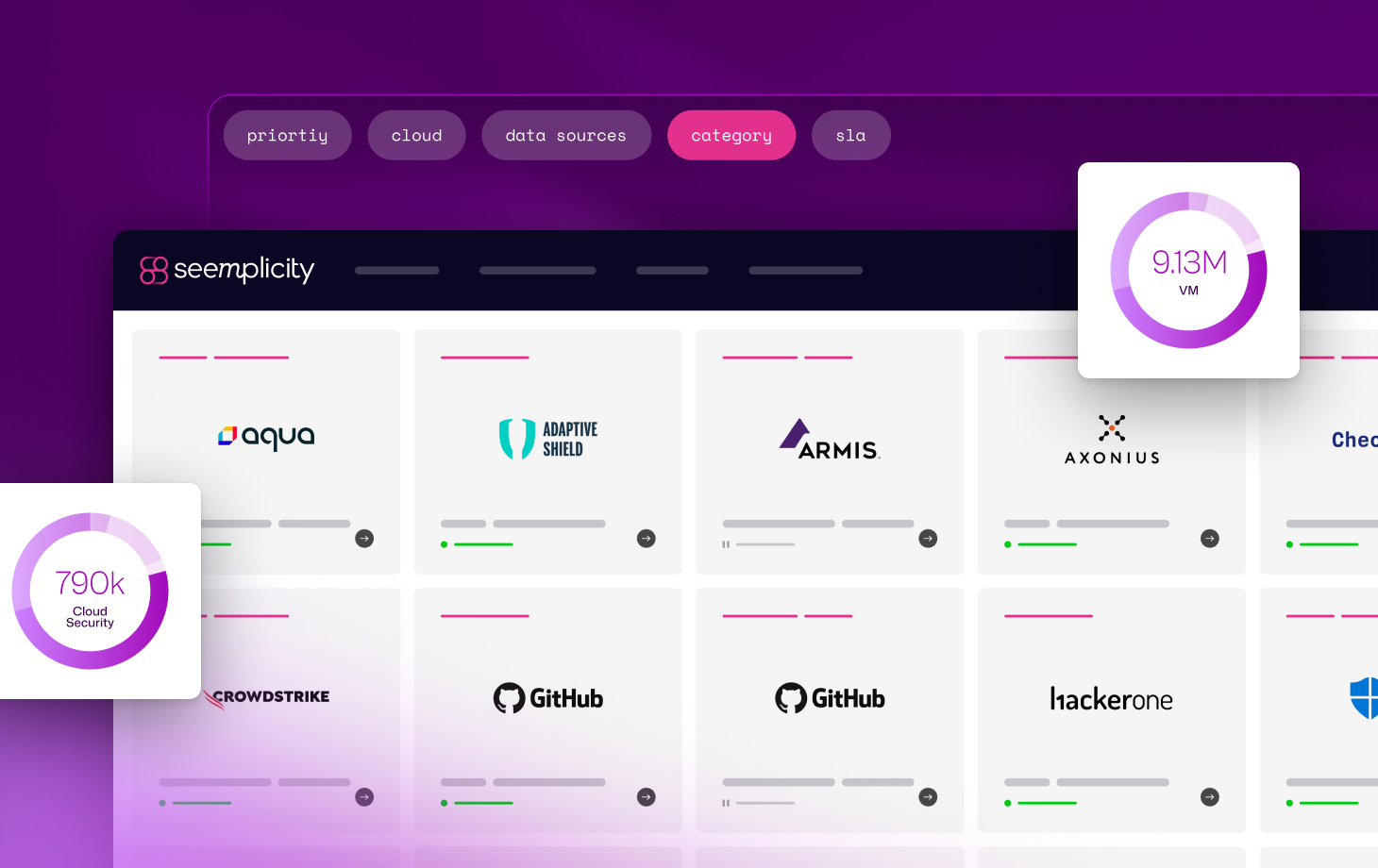
Aggregate application vulnerabilities, misconfigurations, and exposures. By unifying data from all your scanning sources, you eliminate the gaps created by siloed, point-in-time reporting and create a single, consistent model for AppSec risk data.
Live tracking for OWASP Top 10 and regulatory compliance
Connect security findings to the code and fixer
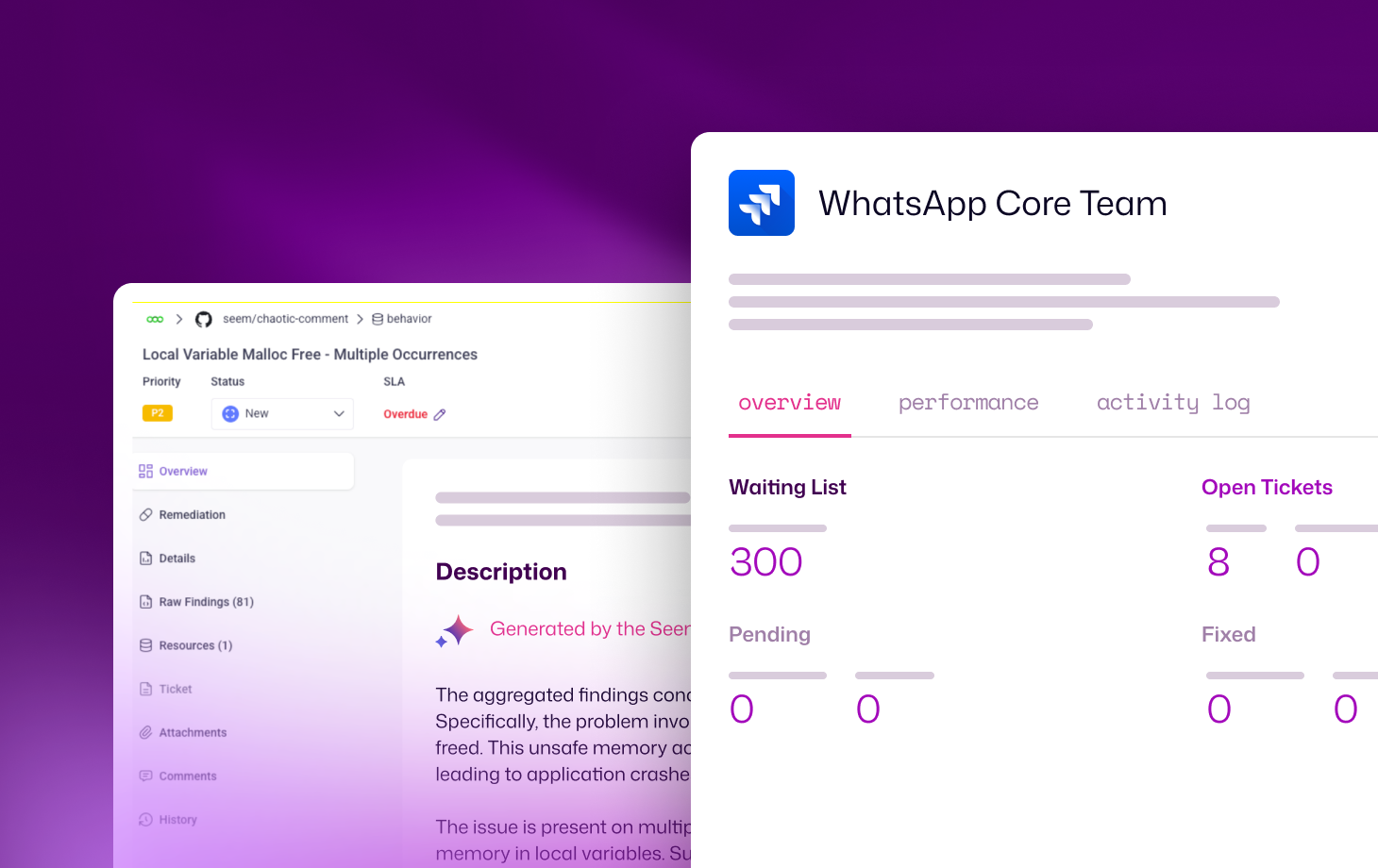
Close the gap between security and engineering. Seemplicity doesn’t just find the bug; it connects it to the specific code repository, line of code (where possible), and developer owner to accelerate time-to-fix and eliminate developer fatigue.
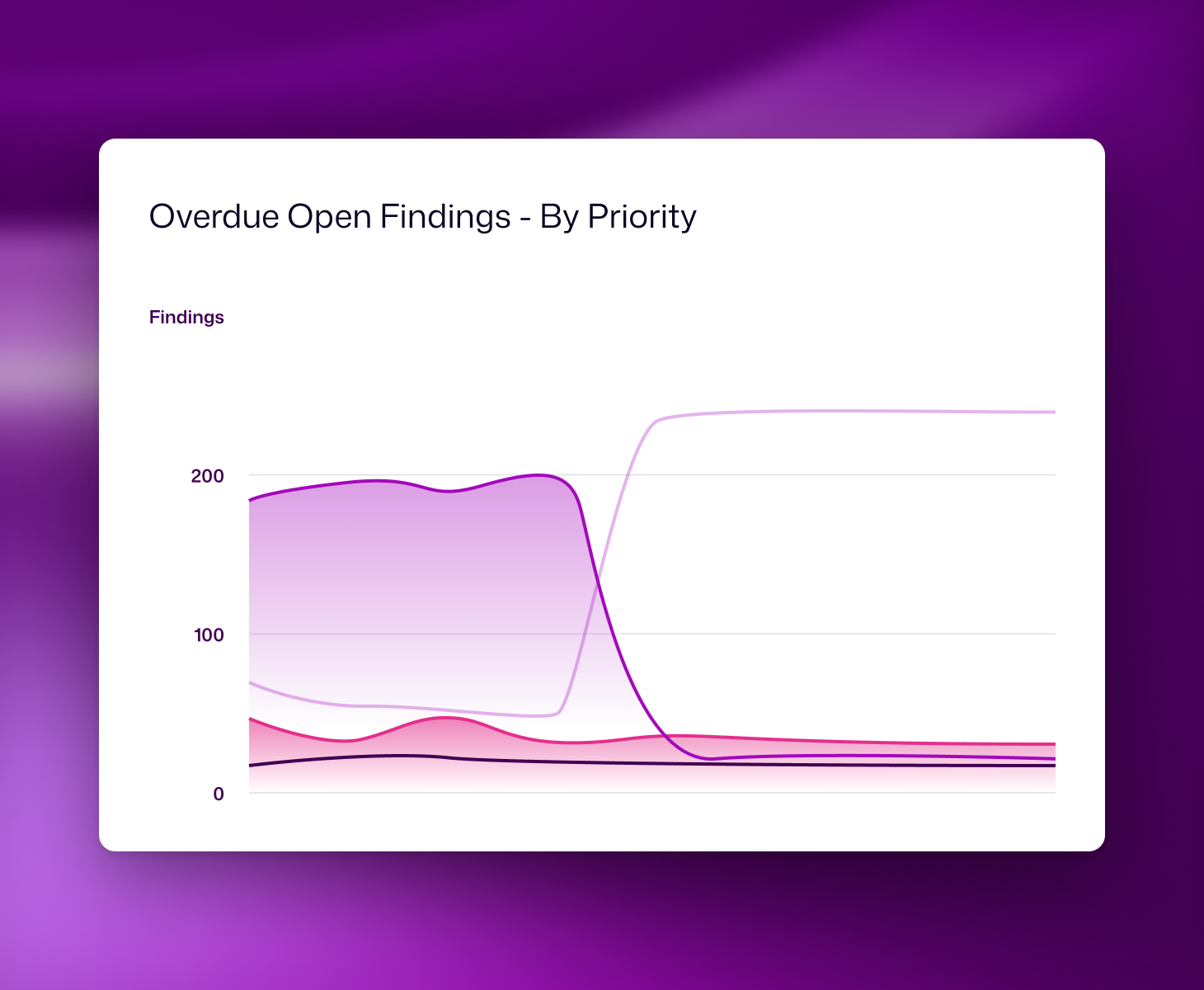
Metrics that prove measurable progress
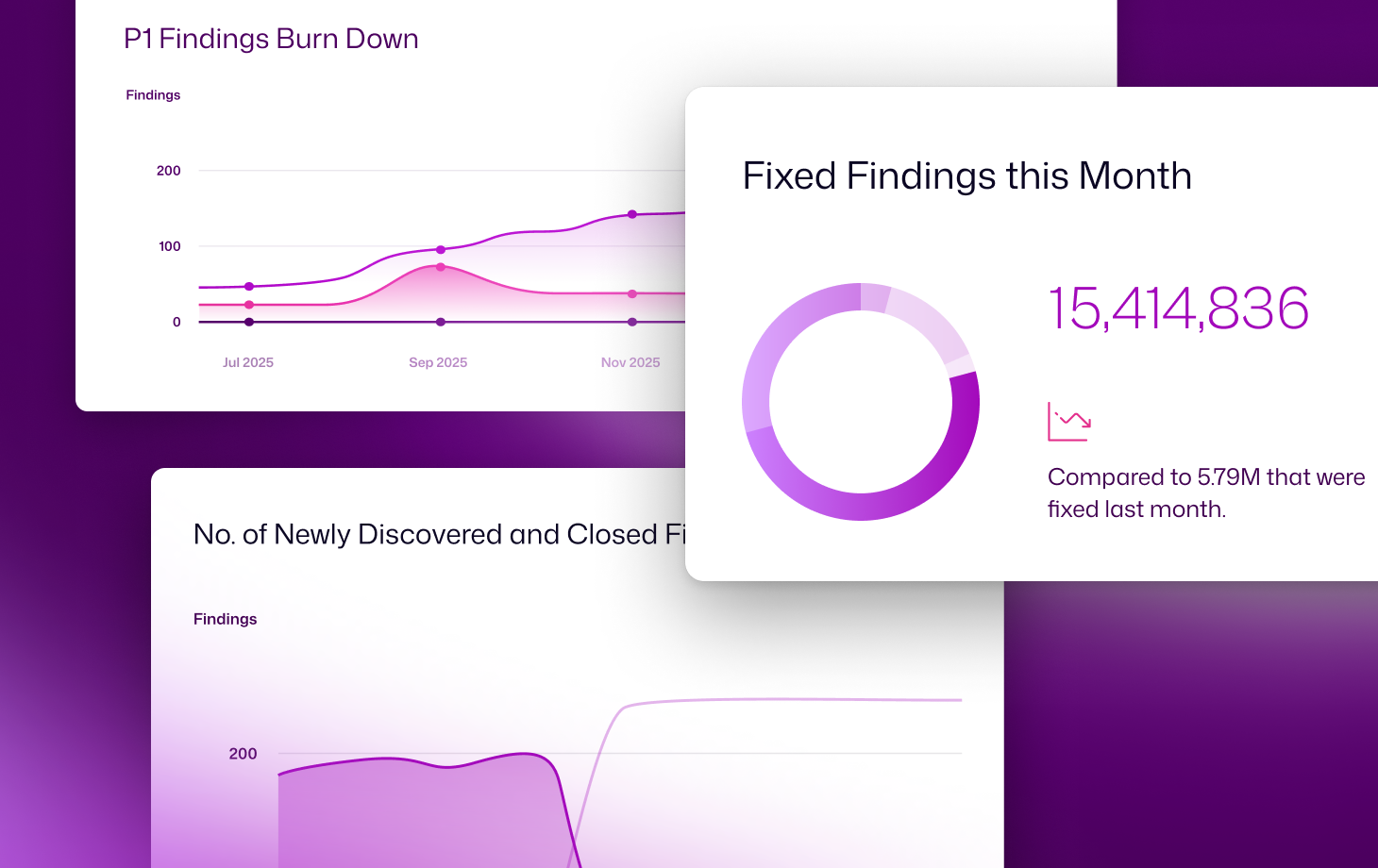
Trade manual data-crunching for live, flexible metrics that show exactly how your application security remediation efforts are shrinking your attack surface and proving impact. Build and share executive-level or deep-dive technical views in seconds.

/research Report
2026 Exposure Action Report
Real exposure management insights based on 2025 customer data. Learn how teams scale remediation, reduce backlogs, and drive measurable risk reduction.
Say Goodbye to
Backlog of vulnerabilities
Misconfigurations
Scattered findings across tools