/TL;DR
Software development moves fast; updates are deployed daily, and new features seem to roll out constantly. For security professionals and developers, this pace brings both opportunities and risks. Building an application security program from scratch can be daunting. Expanding attack surfaces, unclear roles and responsibilities, and an endless stream of vulnerabilities from disparate tools create a complex and challenging landscape to navigate.
So, how do you create an application security roadmap that genuinely reduces risk, supports continuous delivery, and strengthens your security posture? By embracing DevSecOps, you can integrate security into every stage of the software development lifecycle (SDLC), ensuring it becomes a seamless part of the process. This guide breaks it down – from defining what application security really means, to adopting risk-driven processes and using automation to scale efficiently.
You’ll learn:
- What application security encompasses and why it deserves focused attention
- How to distinguish and prioritize exploitable vulnerabilities
- Key principles that transform security from a blocker into a strategic enabler
- Practical workflows, tools, and strategies for continuous improvement
Whether you’re a security leader drafting the first blueprint or a developer seeking to embed security with minimal friction, this application security program roadmap is your foundation for sustainable, effective application security.
The Evolving Challenge of Application Security
The shift from monolithic apps to microservices, from waterfall to agile, and from on-prem to cloud-native architectures has dramatically altered the security landscape. Attack surfaces now include ephemeral containers, third-party APIs, and complex cloud infrastructure. Meanwhile, developers are shipping code faster than ever, sometimes multiple times per day. If your security model still relies on periodic scans or tacked-on policy checks, you’re already behind.
For application security to add value and drive meaningful risk reduction, it needs to be just as agile and adaptable as the environments it protects. That starts by understanding the scope and objectives of a robust application security program.
What Is Application Security? Scope and Focus
At its core, an application security program is a set of processes, technologies, and policies designed to secure software applications from threats across their entire lifecycle – from design and development to deployment and operation.
Key aspects include:
- Identifying security vulnerabilities in code and third-party components
- Prioritizing vulnerabilities based on risk and context
- Mitigating weaknesses proactively
- Embedding repeatable security practices across teams
General vs Exploitable Vulnerabilities
Not all vulnerabilities are created equal. Some are simply potential weak points that might never be exploited, while others pose a real, immediate threat.
General vulnerabilities refer to any identified weaknesses in a system, but they don’t always lead to attacks – often, they’re mitigated by existing safeguards or may not even attract attention from attackers.
On the other hand, exploitable vulnerabilities are the ones to watch out for. These are the flaws that attackers can actively target, often backed by exploit code or easily triggered using common techniques.
Understanding this distinction is central to smart prioritization. You don’t win by trying to patch every weakness; you win by blocking the ones attackers are actively targeting.
Core Principles of an Effective Application Security Program
Building a scalable application security roadmap means embedding several fundamental principles into your approach. Here’s how to shift from checklist compliance to real, risk-based security.
Shift Left… and Right
It’s common advice to “shift security left” by integrating it early in the SDLC. While this is crucial, it’s not enough. Vulnerabilities can emerge at any stage, from design to production, making it essential to take a more holistic approach to application security.
Shift left
Integrating security early in the development pipeline helps catch issues before they become bigger problems. Use tools like Static Application Security Testing (SAST) and Software Composition Analysis (SCA) within your CI/CD pipeline to flag risky code and vulnerable dependencies before they’re deployed. By addressing problems during development, you save time, reduce costs, and increase overall security.
Shift right
Security doesn’t stop when the code ships. It’s critical to monitor applications after deployment to detect vulnerabilities that only appear in runtime. Use tools like Dynamic Application Security Testing (DAST), Breach and Attack Simulation (BAS) and API Security Testing. These provide real-time insights into how the application behaves in production, identifying threats that static testing might miss. Feed these insights back into earlier stages of development to refine your threat models, improve detection capabilities, and create a more resilient system.
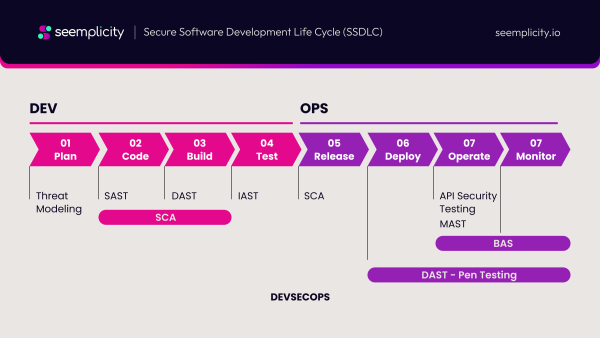
The result: You create a proactive, continuous feedback loop, designing systems that are inherently harder to break instead of putting out fires after the fact. This ensures that security is not just a one-time check but an ongoing, integrated process.
Risk Prioritization
If every vulnerability is “critical,” nothing gets fixed. Risk prioritization is the backbone of modern application security. By focusing on what matters most, teams can allocate their resources efficiently and address the vulnerabilities and exposures that pose the greatest risk, ensuring stronger and more targeted security overall.
Context matters
Don’t blindly chase CVSS 10.0 vulnerabilities just because they’re labeled as high severity. The impact of a vulnerability depends on where it exists and how it could be exploited. For example, a high-severity flaw buried in an internal, non-critical system might pose minimal risk, whereas a medium-severity issue in a public-facing API holding sensitive customer data could have far more serious consequences. Always evaluate vulnerabilities within the broader context of your system’s architecture and data exposure.
Risk scoring
Combine technical severity, environmental exposure (is the asset public-facing or protected?), and business value (what’s the impact if it’s compromised?). Leverage structured databases such as CISA KEV and VulnCheck KEVto identify known exploited vulnerabilities and utilize predictive models like the Exploit Prediction Scoring System (EPSS) to assess exploitation likelihood. This approach provides a more comprehensive understanding of risk, enabling informed decision-making.
Automation
The sheer volume of vulnerabilities combined with the rapid rate of change makes it nearly impossible to manage manually. Automated workflows for triage, routing, and tracking are no longer a luxury – they’re a necessity for staying ahead.
Here’s how automation can help streamline your operations:
- Aggregate findings from all your tools into one centralized source of truth, ensuring nothing falls through the cracks.
- Remove noise by automating deduplication, so your team isn’t bogged down with redundant findings.
- Prioritize effectively with automated contextual enrichment to ensure vulnerabilities are addressed based on their impact.
- Streamline vulnerability management workflows by automating ticket assignment, getting the right findings to the right people.
- Define SLAs based on the severity of vulnerabilities and the criticality of assets, and let automation flag or escalate missed deadlines to ensure nothing is overlooked.
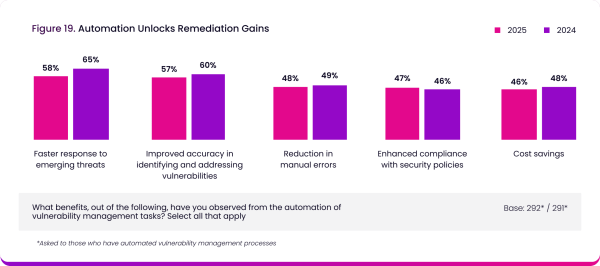
The 2025 Remediation Operations Report shows that with automation handling the repetitive and time-consuming work, your skilled teams can focus their attention on high-priority issues and respond to threats faster.
Cross-Team Collaboration
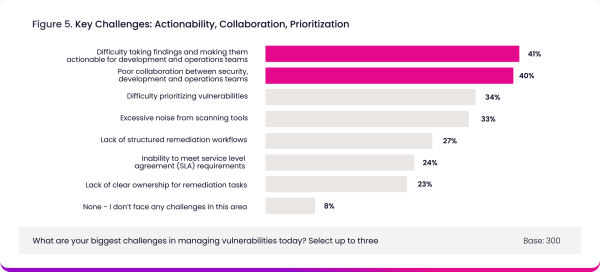
Great application security isn’t just about tools or policies; it’s about fostering collaboration between people. The 2025 Remediation Operations report revealed that the two biggest challenges in managing vulnerabilities are concerned with cross-team collaboration. Security, development and operations teams must work together seamlessly to build and maintain secure applications without slowing down delivery.
Integrate actionable security context
Ensure developers have access to relevant security insights directly within the tools they already use, such as Jira and ServiceNow. This integration prevents critical issues from being overlooked and keeps workflows efficient.
Offer pre-approved secure code patterns
Provide developers with pre-approved secure coding templates and patterns to minimize friction and reduce the time spent solving repetitive security challenges. This empowers them to write secure code faster and more consistently.
Create strong feedback loops
Establish clear communication channels and continuous feedback loops across teams. This ensures everyone stays aligned, the status of security improvements is transparent, and security becomes a shared team goal rather than an isolated responsibility.
When implemented effectively, security should empower teams rather than impede the rapid delivery of software. By embedding security in the development process and fostering collaboration, organizations can achieve both speed and safety.
Identifying Exploitable Vulnerabilities
It’s easy for vulnerability management to become a game of whack-a-mole, drowning security teams in noise. How do you zero in on the issues that truly matter?
Traditional vs. Data-Driven Approaches
Traditional
- Periodic scanning: Regular static and dynamic scans are used to flag known vulnerabilities in an application. These scans are essential for catching common issues but often lack the ability to identify deeper, more nuanced problems unique to your business.
- Manual pen tests: Experts conduct in-depth penetration tests to uncover complex, business-specific flaws that automated tools might miss. While highly valuable, these tests are time-consuming and typically only conducted periodically, leaving gaps in coverage.
These traditional methods form the backbone of application security and have their place in any strategy. However, they often produce large volumes of data, much of it redundant, which can overwhelm teams and lead to alert fatigue.
Data-Driven
Modern programs use automation, threat intelligence, and analytics to sharpen their focus.
- Automated scanners like Wiz, Rapid7, and Snyk deliver broad, continuous coverage across codebases and cloud infrastructure.
- Threat intelligence from public feeds and exploit databases like CISA KEV and VulnCheck KEV helps teams know which vulnerabilities have active exploits in the wild.
- Predictive scoring (e.g., EPSS) uses machine learning and real-world attack data to estimate which flaws are most likely to be exploited next.
This allows security professionals to concentrate on the vulnerabilities that pose the greatest risk to business operations, rather than addressing every single one.
Vulnerability Risk Scoring Systems
It’s not just about “high,” “medium,” or “low.” Effective vulnerability management requires going beyond basic CVSS scores with hybrid approaches that provide a more comprehensive view of risk:
Combine CVSS with other scoring methods
CVSS provides the technical severity of a vulnerability, but its value increases when paired with additional scoring systems like EPSS (Exploit Prediction Scoring System) and Known Exploited Vulnerabilities catalogs such as CISA KEV, or VulnCheck KEV. Together, these tools help you prioritize vulnerabilities based not only on their severity but also on their real-world impact and likelihood of exploitation, ensuring you focus on the most critical and actively exploitable threats.
Asset context
Enhance risk scores by overlaying them with critical information about your assets, such as their value to the organization, the sensitivity of the data they handle, and their exposure level. This added layer of context allows you to prioritize threats not just based on generic risk scoring systems, but in the unique context of your organization’s environment. By understanding which assets are most critical and exploitable, you can focus on securing the systems that matter most to your business operations and overall security posture.
By incorporating these elements, you transform your application security roadmap from a basic checklist into a robust, proactive risk management strategy that aligns with your organization’s goals and priorities.
Tools and Technologies for Your Application Security Roadmap
You can’t build a modern security program without the right tools to support your efforts. Key components that ensure effectiveness and efficiency include:
Automated vulnerability scanners
These tools are essential for identifying and addressing weaknesses across your entire ecosystem, ensuring your systems remain secure. They specialize in covering various critical areas, including source code through Static Application Security Testing (SAST), software dependencies with Software Composition Analysis (SCA), deployed applications via Dynamic Application Security Testing (DAST), and cloud environments to detect potential misconfigurations. By automating vulnerability detection, these scanners provide continuous monitoring, faster identification of risks, and actionable insights.
Threat intelligence feeds
Real-time data on emerging threats, active exploits, and the likelihood of future exploits is essential to stay ahead of attackers in today’s ever-changing cybersecurity landscape. These feeds provide valuable insights into the latest vulnerabilities, malware campaigns, malicious activity, and the probability of specific threats being exploited. By leveraging this information, your team can proactively identify potential risks, strengthen defenses, prioritize responses to critical threats, and better anticipate future attacks, ensuring a more secure environment for your organization.
Remediation Operations platforms
A critical component of any application security roadmap, Remediation Operations (RemOps) platforms play a pivotal role in streamlining the process of addressing vulnerabilities while providing the visibility needed to drive continuous improvement across the organization. These platforms aggregate and consolidate findings from multiple vulnerability scanning tools, eliminating duplicate results and ensuring teams focus only on the most relevant issues. By enriching data with the necessary context—such as severity, business impact, and remediation guidance—these platforms deliver actionable insights to the right teams at the right time, reducing manual effort and significantly improving efficiency. Additionally, their built-in dashboards and robust reporting capabilities empower organizations to track progress in real-time, identify trends, and maintain visibility across the entire program lifecycle. Stakeholders, auditors, and cross-functional teams can easily assess program health and ensure compliance with regulatory requirements. By creating a centralized hub for vulnerability management, Remediation Operations platforms not only enhance collaboration and accountability but also help organizations build a more proactive and resilient security posture.
To learn more about how Seemplicity’s RemOps platform can streamline your application security efforts and enhance your remediation operations, read our solution one-pager here.
Stay updated on Seemplicity blog
Subscribe today to stay informed and get regular updates from Seemplicity.




